U-PROX MPX LE
New powerful dodo-free security center with Ethernet, Wi-Fi, LTE and two SIM cards
New powerful wireless security center with Wi-Fi, LTE and two SIM cards

wireless devices
security zones

Reliable communication with automatic channel switching
security groups
repeaters









Automation for protection and comfort. The security system only counteracts threats - staying at home, in the office and at work goes to a new level.


Our U-PROX PIR Cam motion detectors have the function of verifying alarms and taking photos of objects that fall within their range. When motion is detected, the detector instantly activates the built-in camera, which takes a picture of the object. The user receives a photo or a series of photos in case of an alarm or on request from the app.
The U-PROX security system is characterized by reliable communication. The security center has two receivers operating simultaneously. Any device in the system operates in the notification mode, and the transmission occurs immediately when an event occurs. In addition, the devices support radio wake-up technology. The communication is two-way, encrypted with a 256-bit key, and imitation-resistant, which makes it impossible for an intruder to replace the detector or send the same data packet.

Supporting 8 radio signal range extenders with automatic selection of the best notification route, MPX enables the system to protect not only apartments and private houses, but also large facilities such as multi-storey office buildings and factories, and events are always received on time, even in difficult conditions.
security teams
security zones
users
radio key fobs
automation devices
repeaters
Photos and videos
Flexible system management, instant notifications and key features help take your safety and comfort to the next level
Contact partner companies to purchase or install security and automation devices.
Become an official distributor, reseller or installer of U-PROX security and safety systems.
| Security groups (Partitions) | 30 |
|---|---|
| Users | 250 |
| Wireless devices in the system |
250 zones for detectors 250 key fobs 30 keypads 150 outputs 8 radio repeaters |
| Battery backup | 2500 mAh battery, up to 24 hours (2G/4G only) |
| Power | 12V, 0.35 A |
| Radio frequency |
Two wireless ISM interfaces, with multiple channels and speeds: ITU region 1: 868.0...868.6 MHz (EU, UA), 869.0...869.4 (MA), 20 mW max, distance - up to 4800m (in open space); ITU region 3 (AU): 916.5...917 MHz, 20 mW max, distance to devices - up to 4800 m (in open space). |
| Communication | Two-way, encrypted, with sabotage (jamming) detection. The encryption key is 256 bits |
| Connection |
Computer network - Wi-Fi 2.4GHz, LTE modem for backup. For initial setup - BLE 2.4GHz Two-way encrypted communication, encryption key - 256 bits |
| Wi-Fi | 2.4 GHz, 802.11b/g/n, Open/WPA/WPA2/WEP 14 dBm for 802.11n MCS7, 20 dBm for 802.11b |
| LTE/GSM modem |
LTE-FDD Cat 1 - B1/B3/B5/B7/B8/B20/B28, GSM - B2/B3/B5/B8, 2 SIM cards |
| Operating temperature range |
-10°C ... +55°C THE BATTERY CANNOT BE CHARGED AT TEMPERATURES BELOW 10°C |
| Permissible humidity | up to 75% |
| Environmental class | II (according to EN 50131-1) |
| Security grade | 2 |
| Dimensions | 167 х 120 х 25.4 mm |
| Case colour | white, black |
| Weight | 0.245 kg |
| Complete set |
1. U-Prox MPX L; 2. Rechargeable 18650 battery (pre-installed); 3. Power supply unit; 4. Short user manual |









U-PROX MPX L is a the center of a wireless security system. It manages a home security system and supports the connection of wireless devices (detectors, keypads, key fobs, etc.) via a radio channel at distances of up to 4800 m. The device interacts with the user and the security company using the Internet (Wi-Fi, Ethernet) and LTE communication for reliability.
The device has two transceivers – 868.0…868.6 MHz with several redundant channels and provides secure, encrypted (256-bit encryption key) two-way radio communication with radio channel sabotage detection. Wireless devices connected to U-PROX MPX L operate according to the notification scheme of data transmission – they notify about events that have occurred, such as motion detector or magnetic contact triggering, and periodically transmit their status, such as battery level, etc. This principle of operation allows you to save battery and reduce the load on the radio channel.
U-PROX MPX L supports photo verification and photo recording of alarms thanks to motion detectors with a built-in U-PROX PIR Cam.
The device has a built-in 2500 mAh battery and can operate for up to 20 hours in the absence of main power.
To interact with users, the device requires Internet access to connect to the U-PROX Cloud service. Using the cloud service and smartphone applications, users can
connect to the U-PROX MPX L for management and configuration.
The U-PROX Cloud service is required to interact with the security system and its maintenance, to receive new software versions of both the security center itself and to
update the software of wireless equipment connected to U-PROX MPX L.
U-PROX MPX L and U-PROX Cloud are designed in such a way that only the minimum required amount of personal data is stored on the cloud service in a secure form, and
communication between the device and U-PROX Cloud takes place via a secure imitation and crypto-resistant channel.
The device can work both autonomously, with the transmission of events to users’ smartphones, and with connection to security companies. The device uses Internet
access to transmit events to security companies. Depending on the device settings, events can be transmitted to the security company directly and/or via the U-PROX
Cloud.
During installation and operation of the device, it is necessary to comply with the “Rules for the technical operation of consumer electrical installations” and the “Rules for the safe operation of electrical installations”.
Installation work must be performed with the power supply switched off. In addition, fire safety rules must be observed when performing any work.
DO NOT DISASSEMBLE THE DEVICE OR ITS POWER SUPPLY UNIT WHILE VOLTAGE IS APPLIED AND DO NOT USE A POWER SUPPLY UNIT WITH A DAMAGED CABLE.
THE DEVICE HAS A BUILT-IN BATTERY. REPLACING THE BATTERY WITH AN INCORRECT TYPE MAY RESULT IN FIRE OR EXPLOSION. DISPOSE OF USED BATTERIES IN ACCORDANCE WITH LOCAL LAWS AND REGULATIONS.
THE BATTERY MUST NOT BE CHARGED AT TEMPERATURES BELOW 10°C; MAKE SURE THAT THE POWER ADAPTER IS CONNECTED.
U-PROX MPX L supports 4G/2G communication. Data transmission speed in 2G is 20–55 kbit/s, and in 4G it can reach up to 10 Mbit/s.
The device works sequentially with two SIM cards, when one of the cards is active, the other is in cold standby.
The device automatically detects the service provider and settings for accessing the mobile network.
Depending on the services provided by the service provider, not only data transfer is available, but also a call to a specific phone number, which can be used to notify users
of an alarm.
IF BOTH SIM CARDS ARE ABSENT FROM THE DEVICE FOR 5 MINUTES, THE DEVICE WILL TURN OFF THE MODEM. AFTER INSTALLING A SIM CARD, THE DEVICE MUST BE RESTARTED.
All U-PROX MPX L models support Wi-Fi 2.4 GHz.
Search and connection to the access point can be performed both locally from the U-PROX Installer mobile application via BLE (Bluetooth Low Energy) channel and remotely
from the U-PROX Installer WEB web portal or the U-PROX Installer mobile application.
DHCP is supported for dynamic IP address acquisition on the network.
The device is powered by a 12 V power supply and is equipped with a standard DC 5.5×2.5 mm connector. This allows the use of alternative power sources or connection of an external uninterruptible power supply or battery.
In the absence of main power, the device switches to power-saving mode and operates from the built-in battery.
In this mode, if there is no Wi-Fi connection, the device turns off Wi-Fi and operates exclusively via LTE.
The constant status display of the device will also be disabled, instead the status will be displayed every 30 seconds.
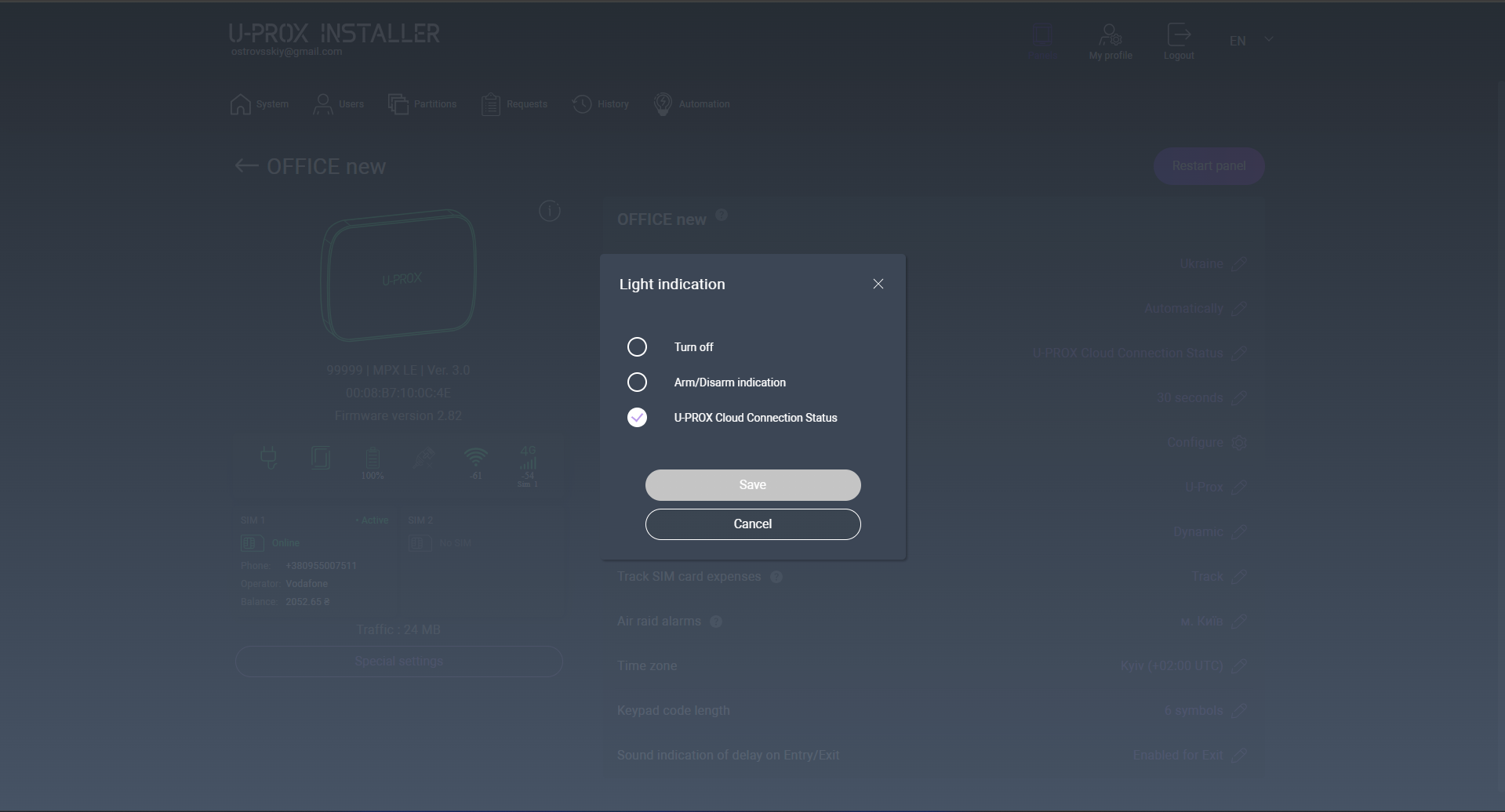
The U-PROX LED indicator on the front panel displays the current device status and can be configured by the user. The following indication modes are available:
• Off – the LED indicator is turned off.
• Cloud connection status – displays the connection status to U-PROX Cloud:
– Green light: connection to U-PROX Cloud is established via at least one communication channel.
– Red light: there is no connection to U-PROX Cloud via any LTE or Wi-Fi channel.
• Security status – displays the system arming status:
– Red light: the system is armed.
– Green light: the system is disarmed.
Flashes green every 30 seconds – indicates that the main power supply is absent, the device is operating in power-saving mode, and the connection to U-PROX Cloud is established via at least one communication channel (available when the Cloud connection status indication mode is enabled).
Flashes red every 30 seconds – indicates that the main power supply is absent, the device is operating in power-saving mode, and the connection to U-PROX Cloud is not available via any LTE or Wi-Fi channel (available when the Cloud connection status indication mode is enabled).
Carefully select the installation location for the U-PROX MPX L wireless security control panel. It must meet the following criteria:
U-PROX MPX L must not be placed:
1. Unscrew the fixing screw.
2. Slide the backplate down and detach it.
3. Place the SIM cards (with PIN request disabled) into the holders.
4. Secure the cable using the cable retainer included in the package.
For the appliance to turn on, simply connect the power supply to the appliance and plug the power supply into a power outlet.
To turn on the appliance without the main power supply connected, press the (6), the indicator light (2) will turn on and the appliance will start booting up.
To turn off the appliance, disconnect the power supply, then press and hold the (6) for 3 seconds until the sound indication and the light indication go out.
BEFORE PERFORMING THIS STEP, THE DEVICE MUST BE CONNECTED TO U-PROX CLOUD.
1. Secure the mounting plate to the surface (for example, a wall) at the installation location using the screws and wall plugs included in the package.
2. Make sure that the power supply unit is connected and secured with the cable retainer.
3. Install the device onto the mounting plate and slide it downward to secure it and lock the tamper contact.
4. Secure the enclosure with the screw included in the package.
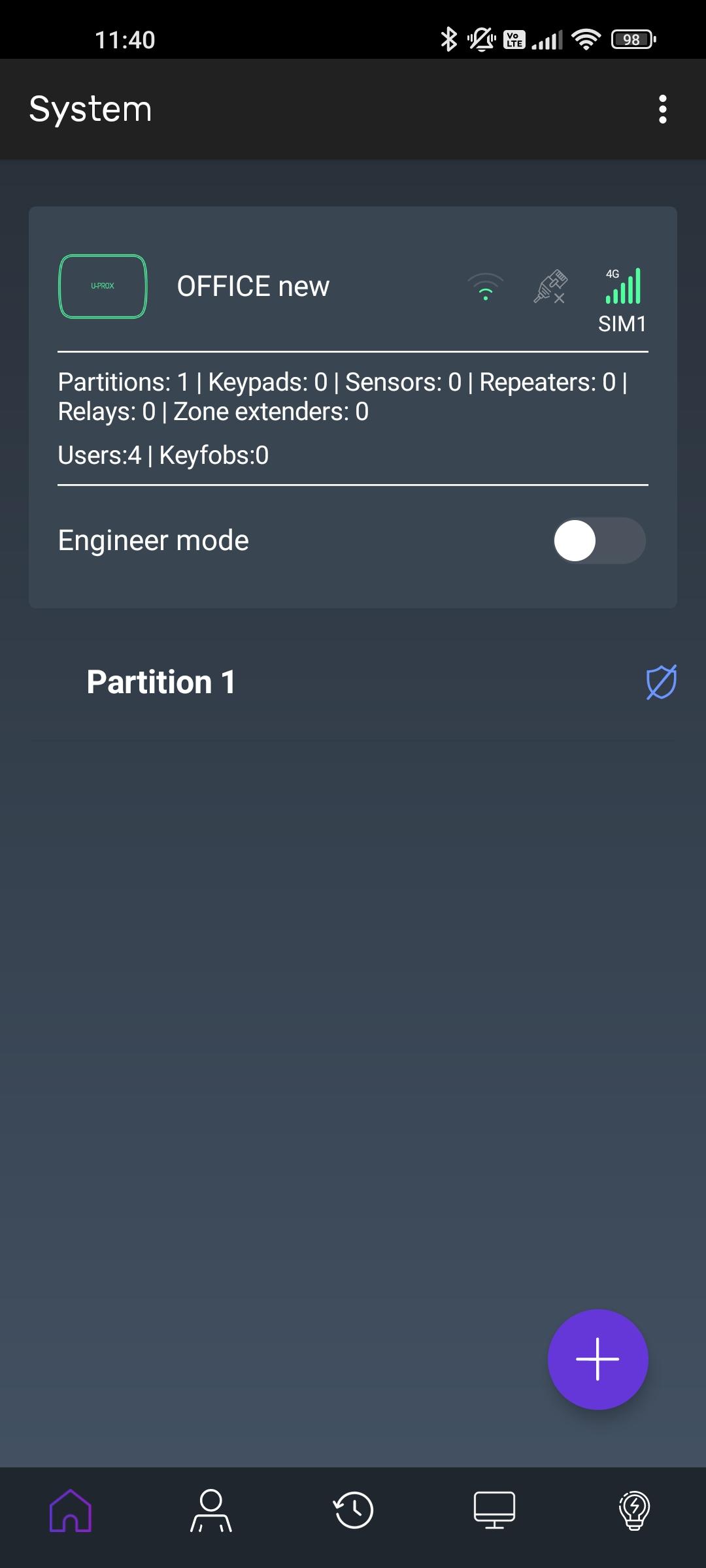
To work with U-PROX devices in the cloud system, two separate applications are used, the functions of which are separated. The first is the U-PROX Home user application for managing the security system and the second is the U-PROX Installer application for configuring U-PROX devices.
The U-PROX MPX L device is configured using the U-PROX Installer mobile application or the U-PROX Installer WEB web portal via the U-PROX Cloud.
To access U-PROX Cloud services, you need to register and create an account. To register an account, use your email address.
The cloud system supports the following account types:
Registration is performed via the U-PROX Installer application or on the U-PROX Installer web portal:
https://web-security.u-prox.systems/
The individual installer can:
To register, send a request to:
The security company administrator can:
Registration is performed via an invitation link that the security company administrator sends to the installer’s email address.
The security company installer can:
Registration is performed via an invitation link that the security company administrator sends to the installer’s email address.
The security company manager can:
Registration is performed via an invitation link that the security company installer sends to the user’s email address.
System management is performed using a separate U-PROX Home user application.
The user can:
Registration is performed via an invitation link that the individual installer sends to the user’s email address.
System management is performed using a separate U-PROX Home user application.
The user can:
This application is used to configure the U-PROX wireless security system. It is intended both for individual users and for engineers of centralized monitoring organizations.
Using a mobile phone, the application allows full configuration of the security system – installation, testing, and calibration of wireless system elements; configuration of security groups; connection to monitoring stations; adding users and granting them rights to control the security system via the U-PROX Home application.
This application is intended for managing the U-PROX wireless security system.
Using a mobile phone, regardless of your location, you can arm/disarm your premises, control home automation devices, and monitor system events via push notifications and event history for a selected time period.
Using this single application, you can manage multiple security systems (for example: an apartment, a country house), each of which may have one or more security groups (for example: house, garage, safe).
The U-PROX Installer web portal is intended for configuring the U-PROX wireless security system. It is intended both for individual users and for engineers of centralized monitoring organizations.
Using a web browser, you can perform full system configuration – installation, testing, and calibration of wireless system elements; configuration of security groups; connection to monitoring stations; adding users and granting them rights to control the system via the U-PROX Home application.
https://web-security.u-prox.systems/
U-PROX Console v2 is software designed for convenient integration of U-PROX devices with monitoring software. It works with most monitoring programs and supports ContactID, SIA DC09, and XML formats.
You can download the U-PROX Console v2 software and the configuration file from the security company administrator’s workspace on the U-PROX Installer web portal.
IF NECESSARY, REGISTER IN THE SYSTEM AS A STANDALONE INSTALLER OR OBTAIN ACCESS AS A SECURITY COMPANY INSTALLER.
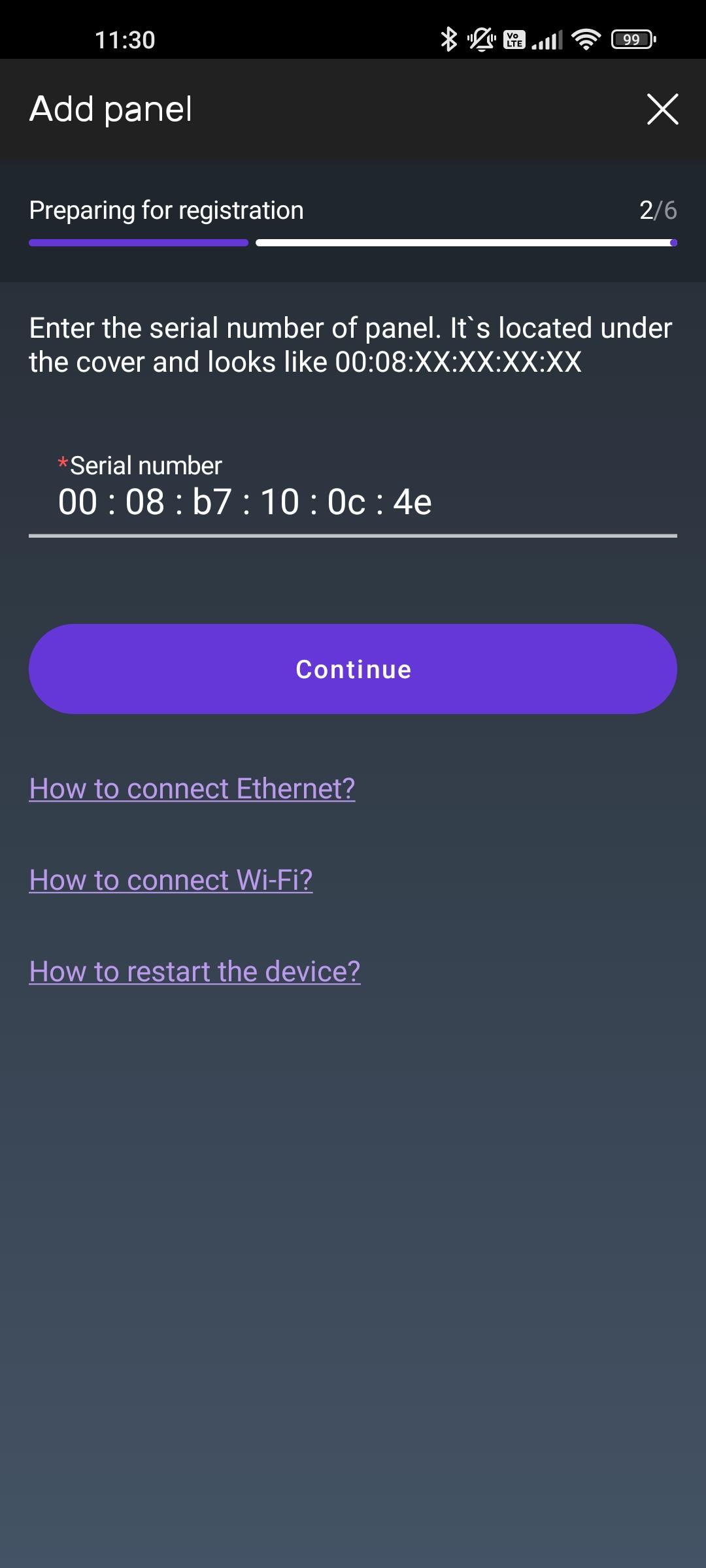
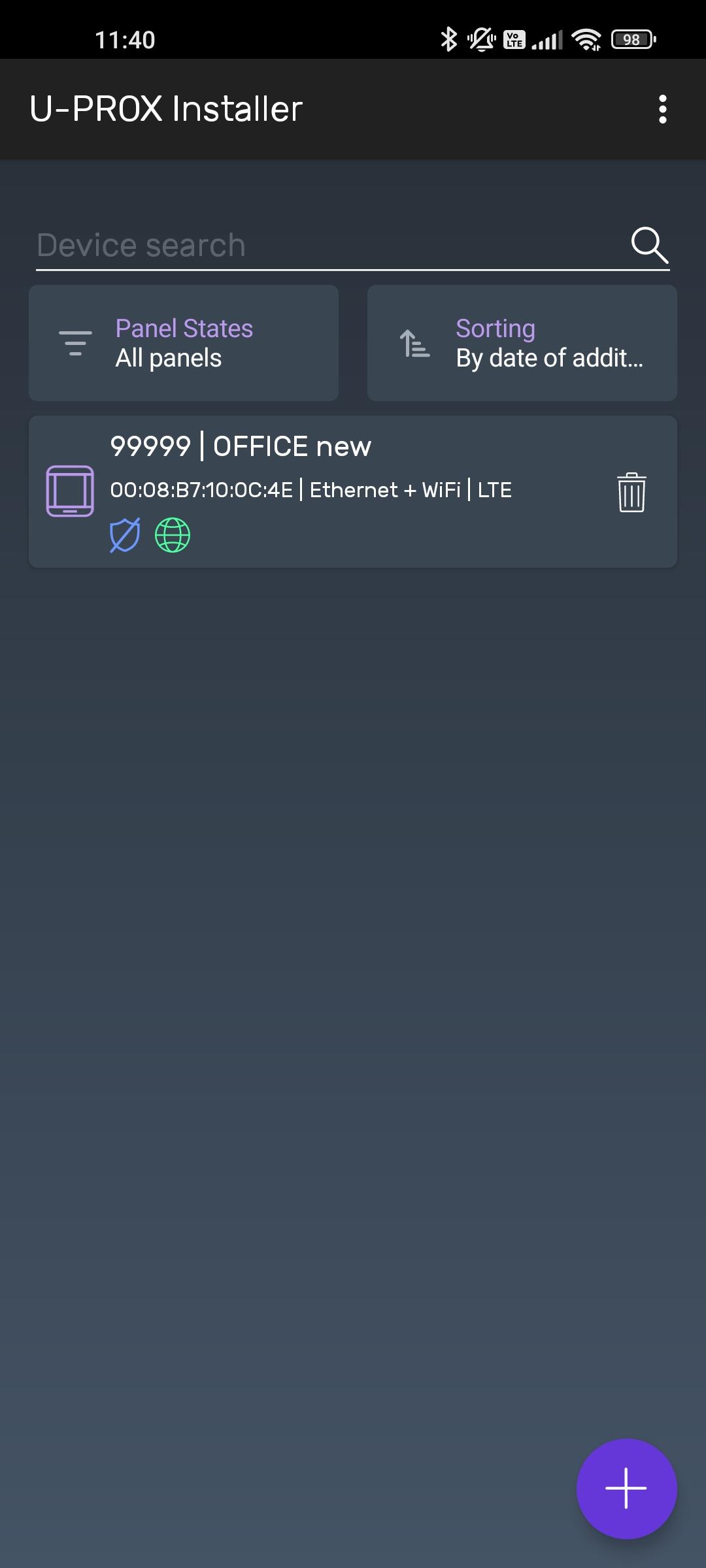
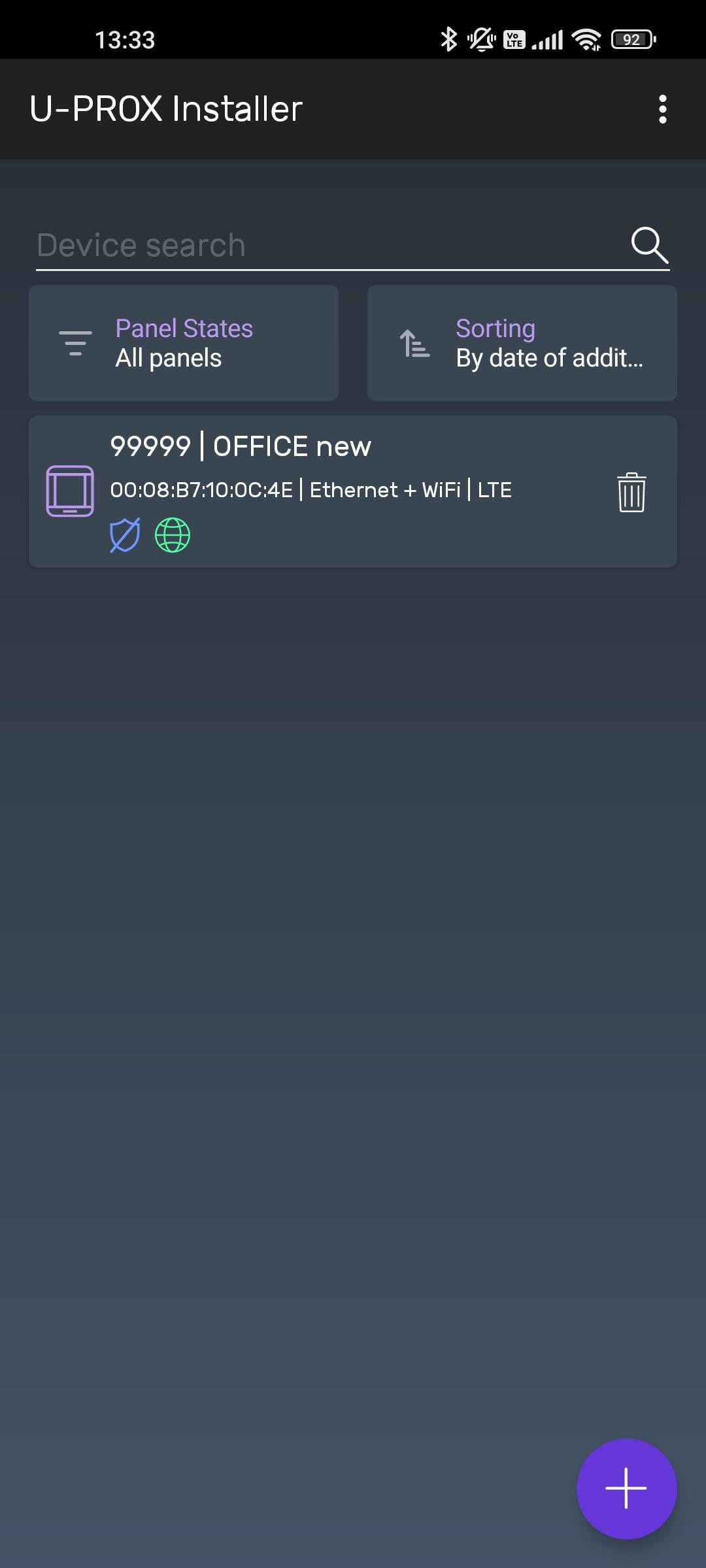
2. Press the (+) button (“Add device”) to add a device

3. When adding a device from the U-PROX Installer mobile application, it is possible to add the security control panel by serial number or find it via Bluetooth:


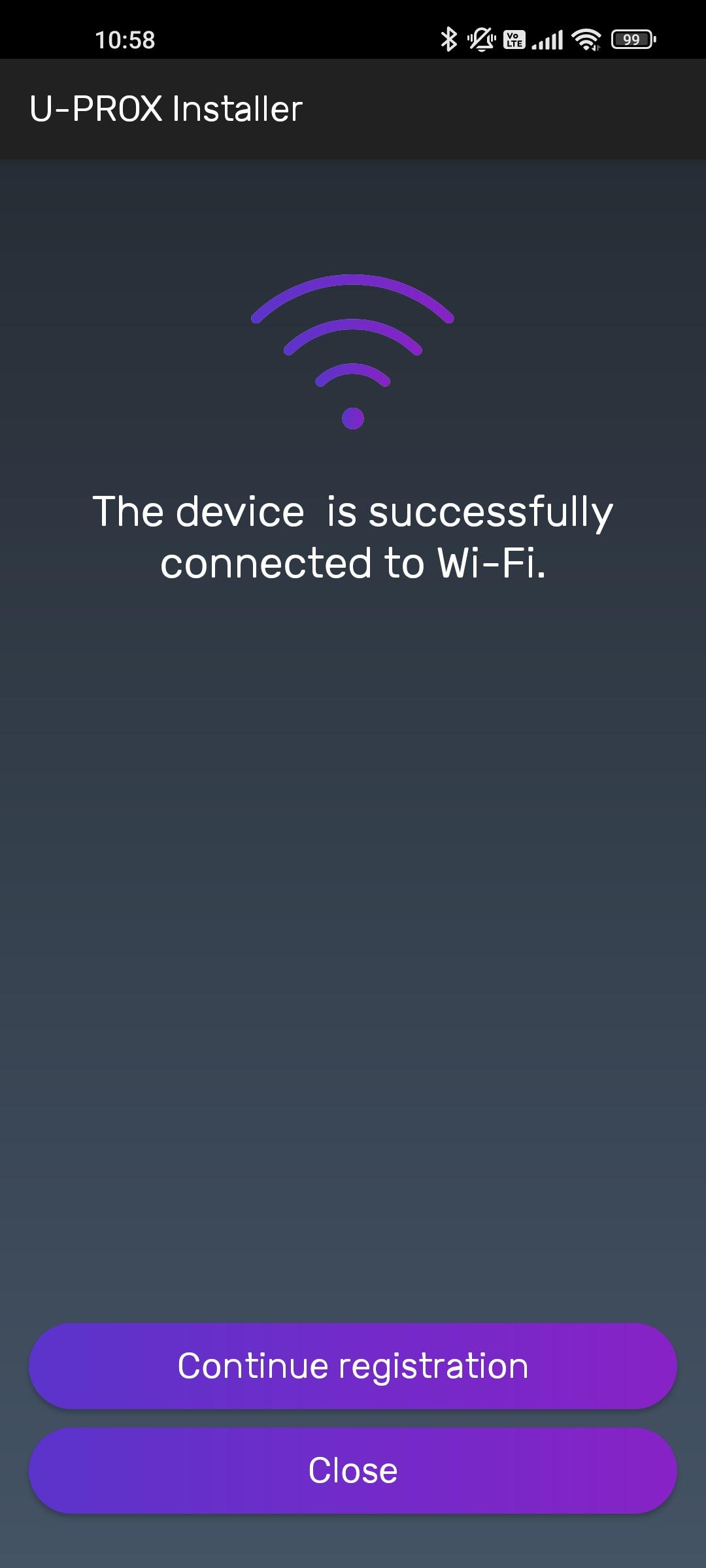
ATTENTION: THE DEVICE OPERATES ONLY WITH WI-FI 2.4 GHz. OTHER WI-FI TYPES ARE NOT SUPPORTED AND WILL NOT BE DISPLAYED DURING SCANNING.
4. When adding a device from the U-PROX Installer WEB web portal, you must enter the serial number of the security control panel. In the U-PROX Installer mobile application, press the “Add by serial number” button for this purpose.
5. The device will be added to the cloud account
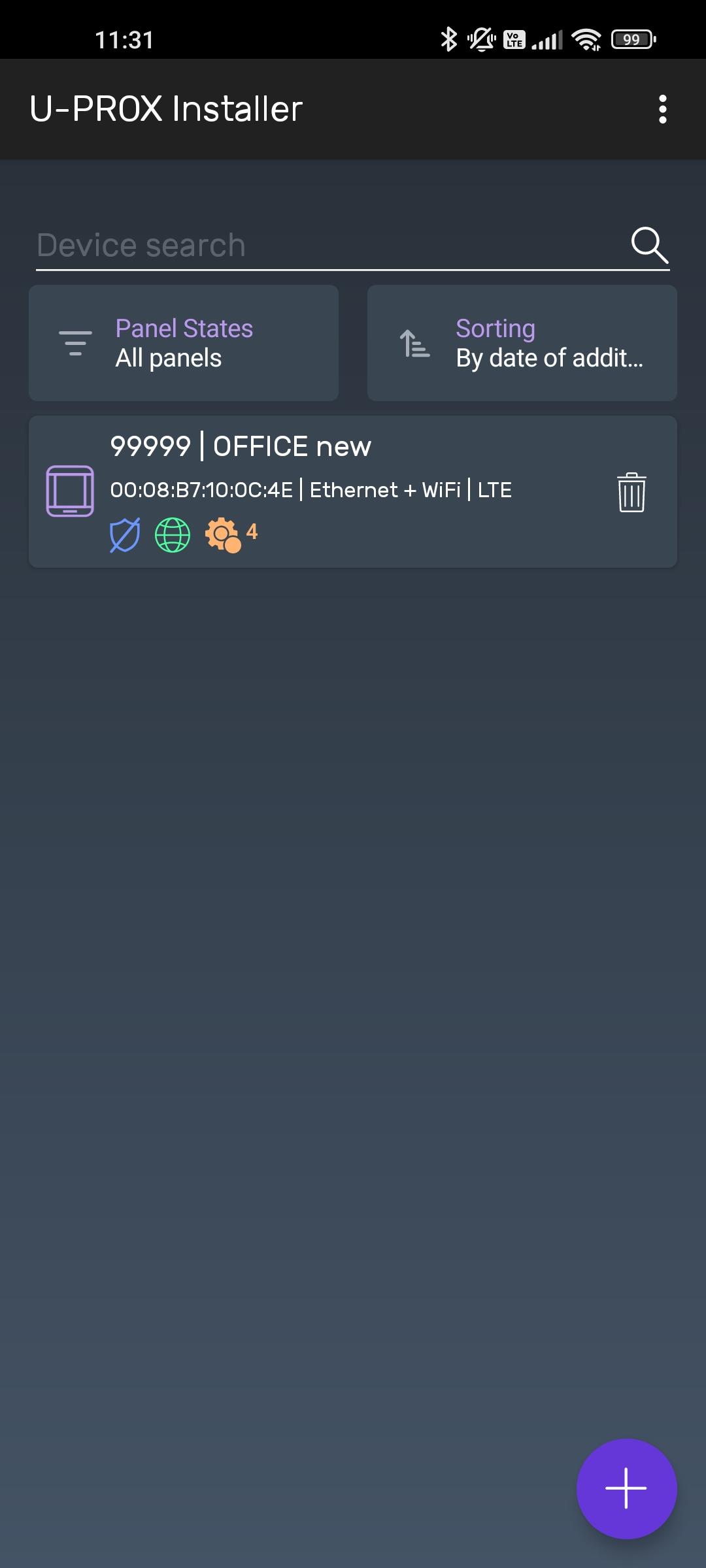
6. The system will navigate to the device list
AFTER SUCCESSFUL ADDING, THE DEVICE IS LINKED TO THE ACCOUNT OF THE SECURITY COMPANY OR THE INDIVIDUAL INSTALLER. TO ADD IT TO ANOTHER ACCOUNT, THE DEVICE MUST BE REMOVED FROM THE PREVIOUS ACCOUNT.
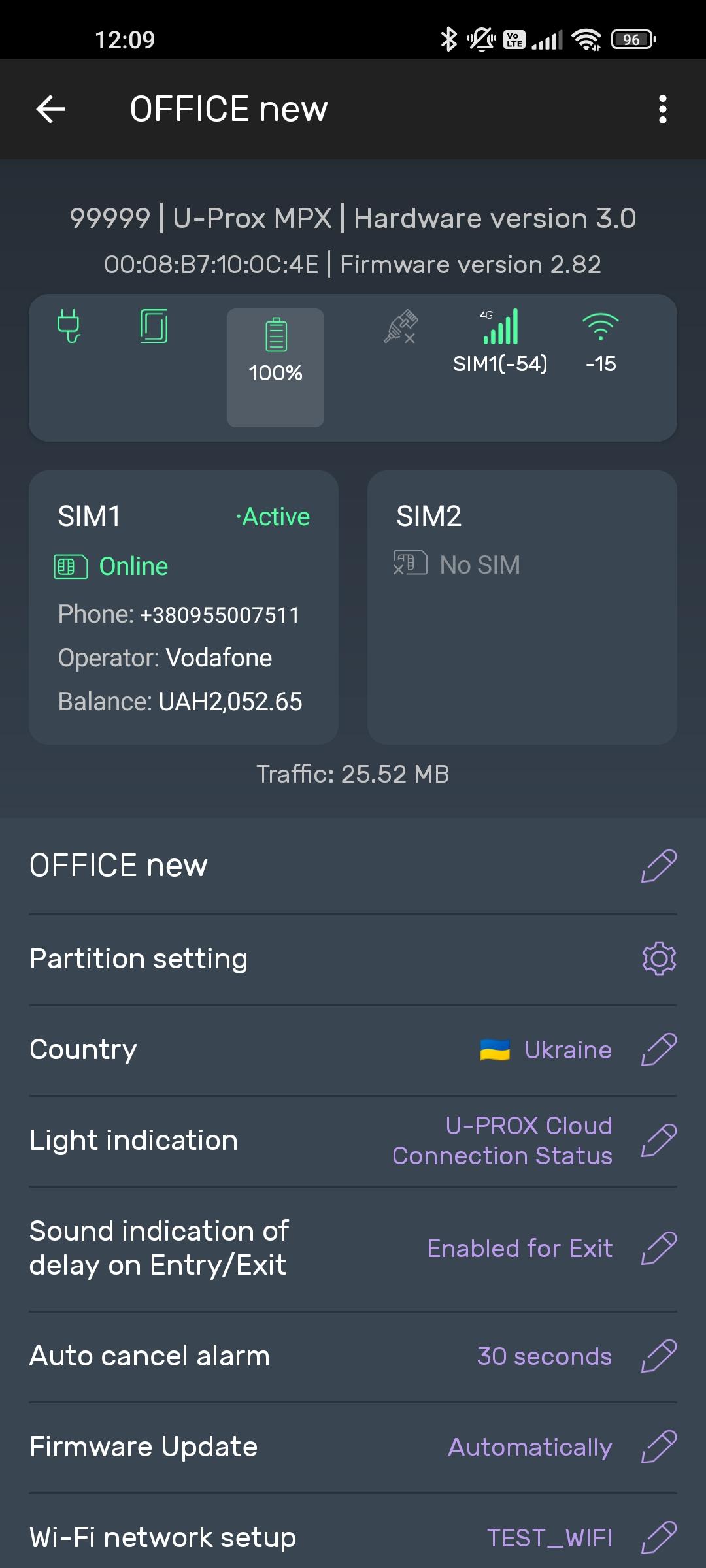
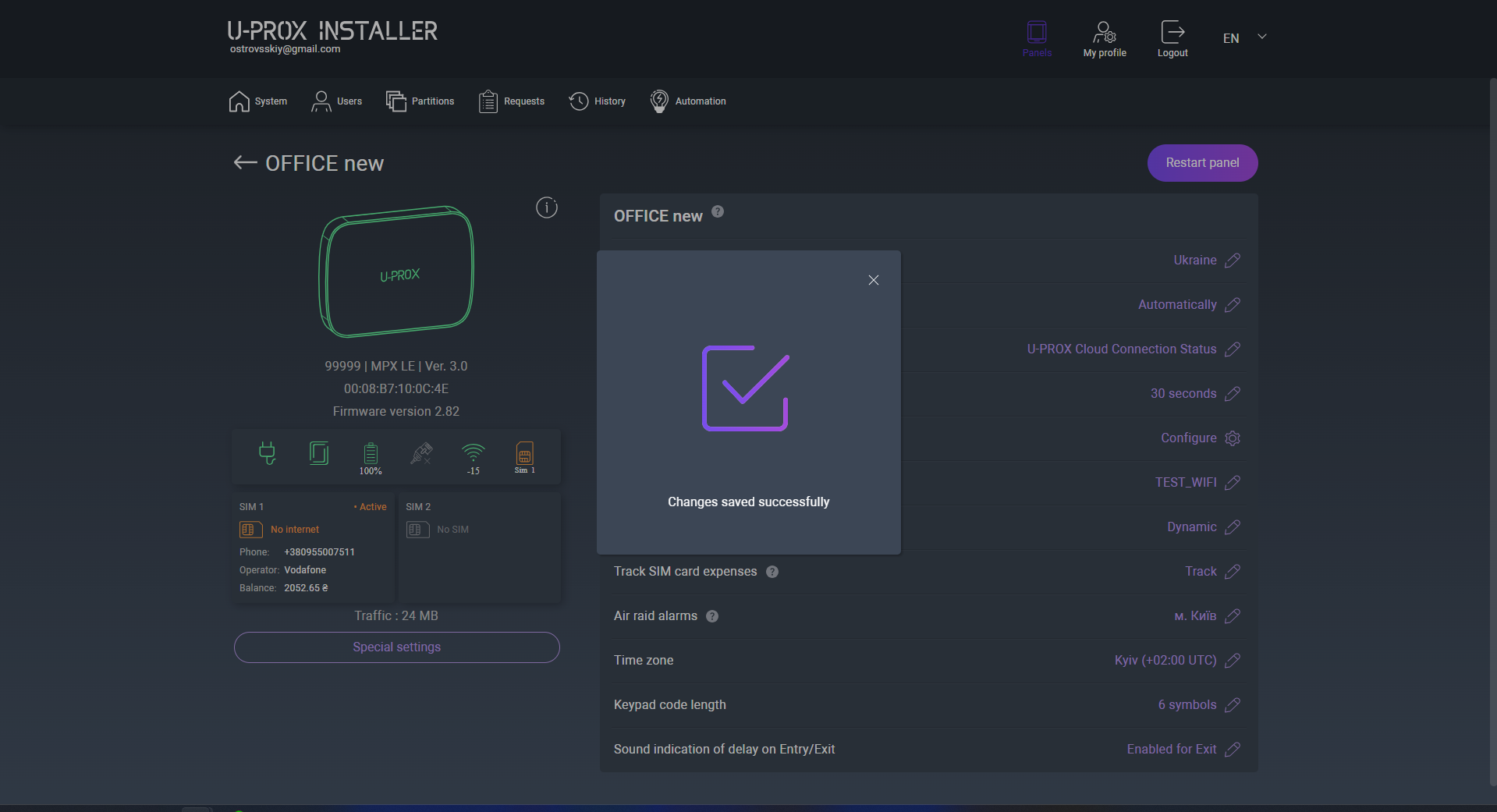
2. Go to the security control panel settings.
3. “Group settings” – go to the section for managing security groups.
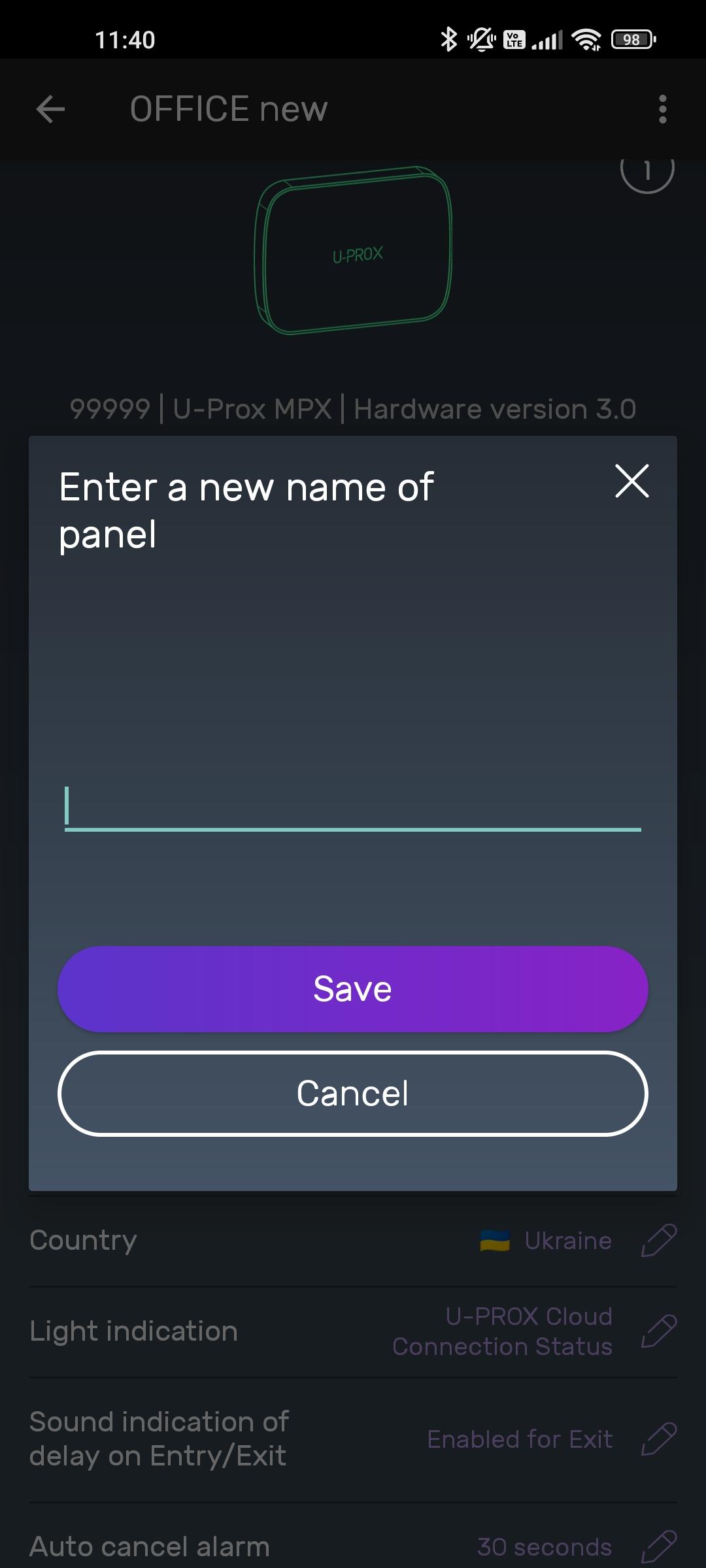
4. “Device name” setting – change the name of the security control panel.
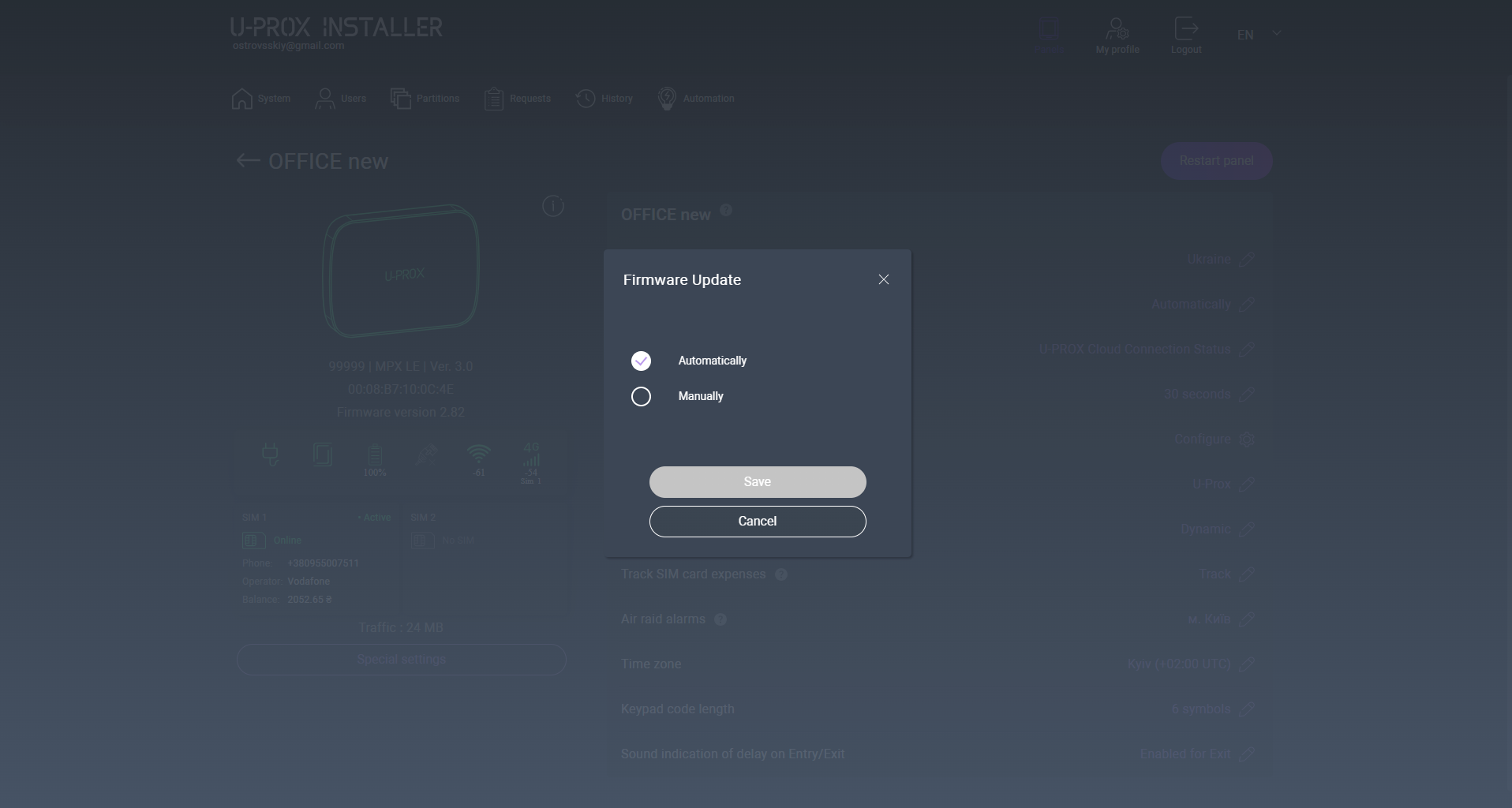
5. “Firmware update” setting – enable or disable automatic firmware updates from the cloud service.
6. “LED indication” setting – enable or disable the indicator on the front panel.
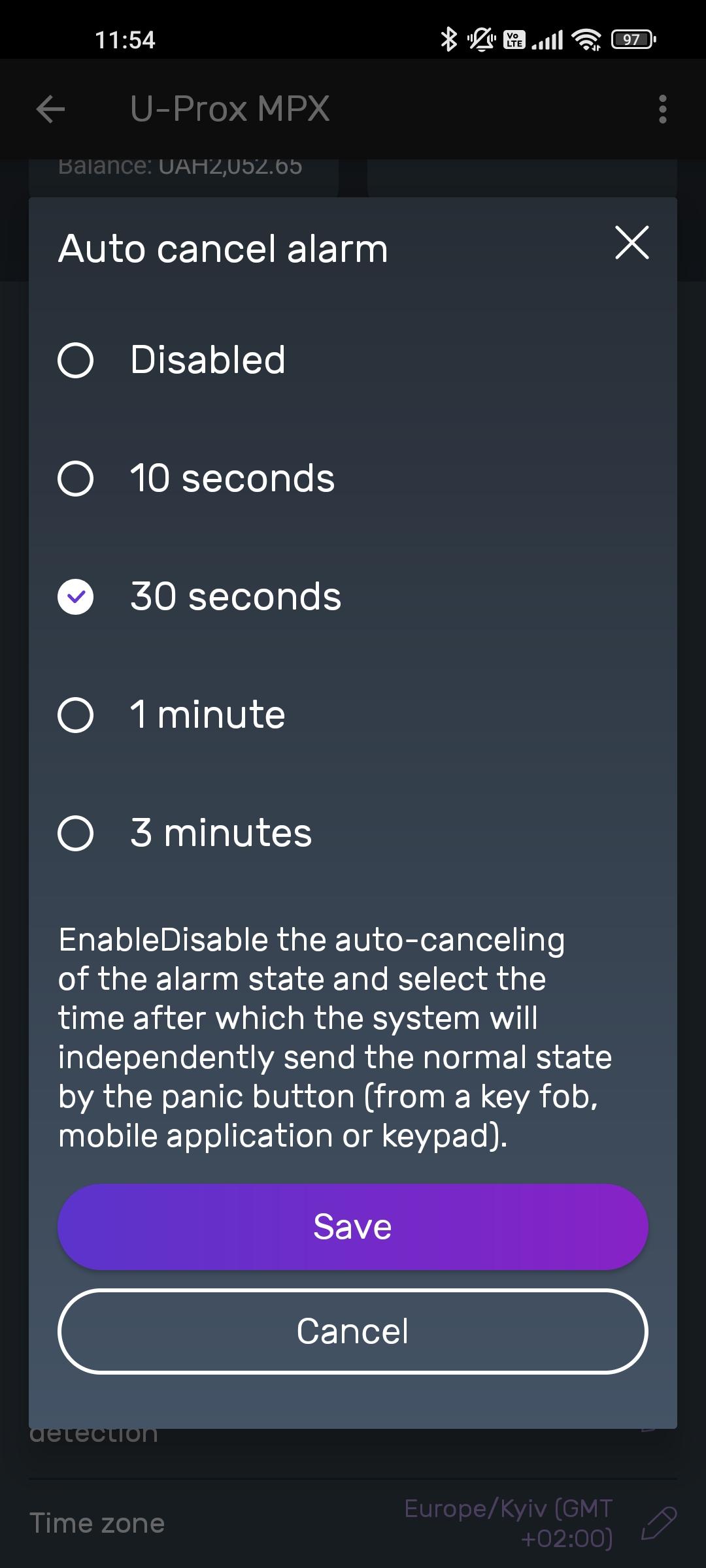
7. “Alarm auto cancel” setting – define whether the alarm is canceled after a specified time, by user action in the application, or after entering a code on the keypad.
8. “Cellular data network” – configure mobile Internet connection parameters.
9. “Wi-Fi network” – configure connection to the wireless network.
10. “Ethernet” – configure wired Internet connection.
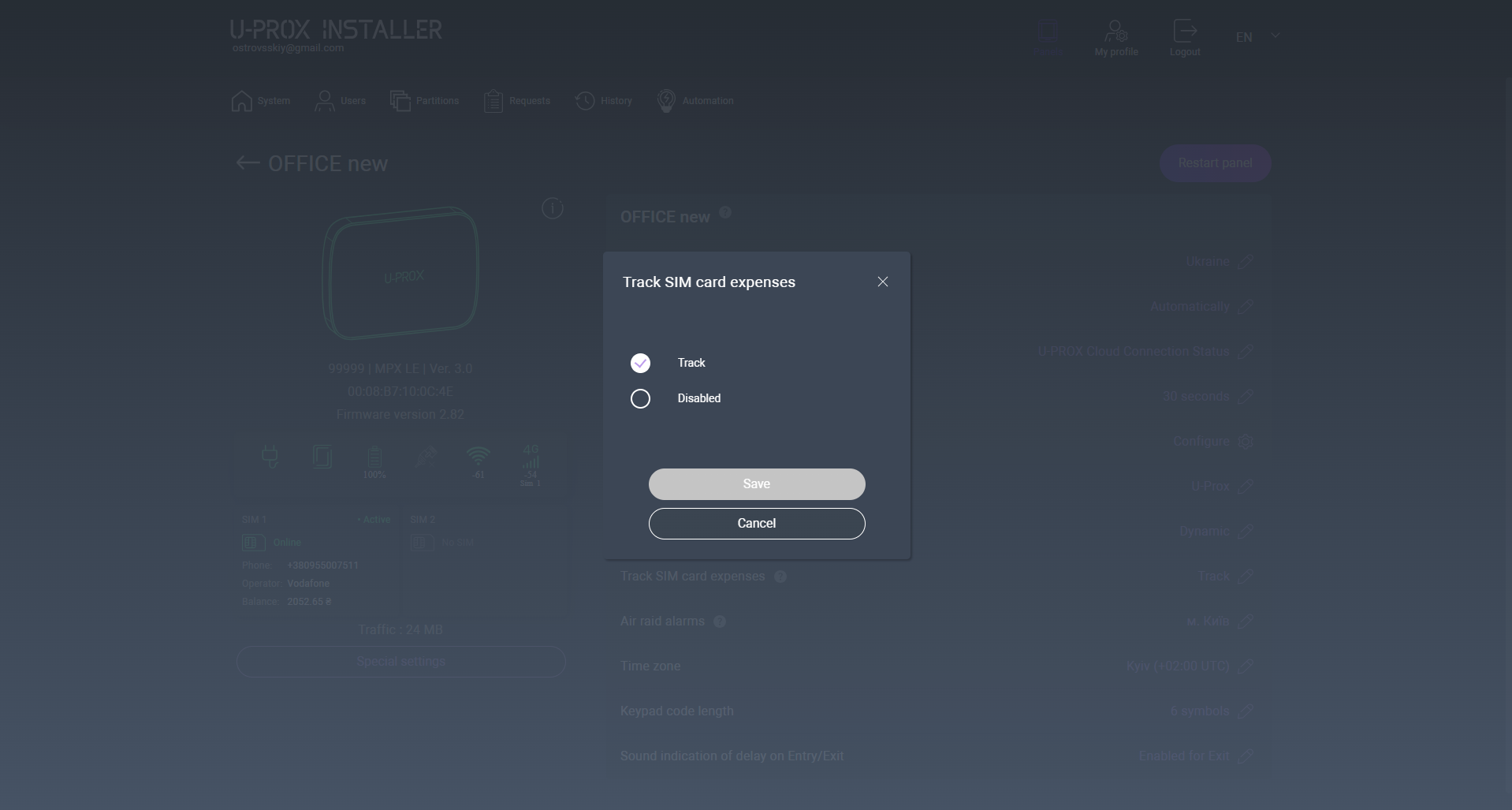
11. “SIM card balance control” – the device periodically requests the remaining mobile Internet balance from the modem.
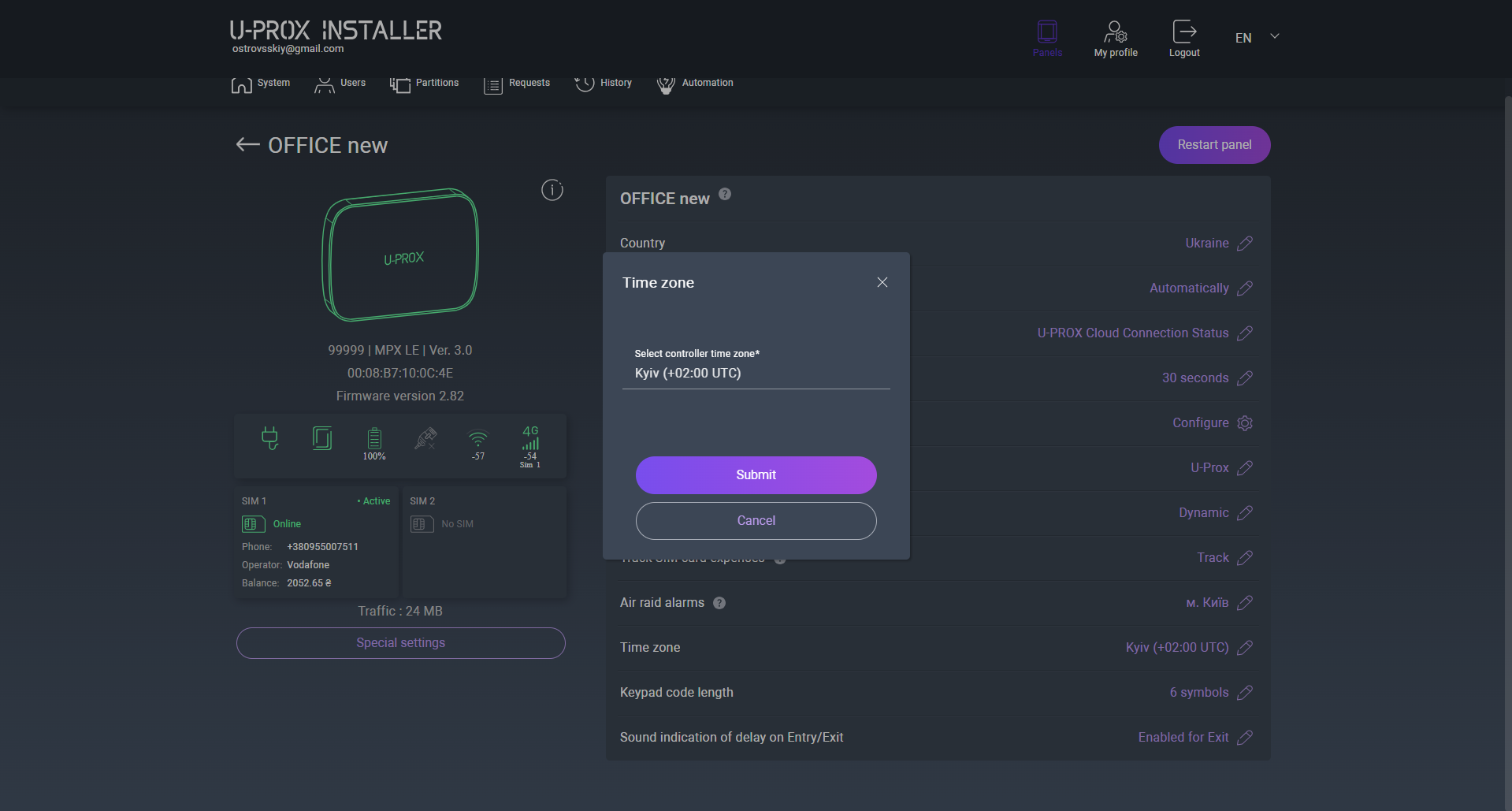
12. “Time zone” – a parameter that defines the offset required to determine local time.
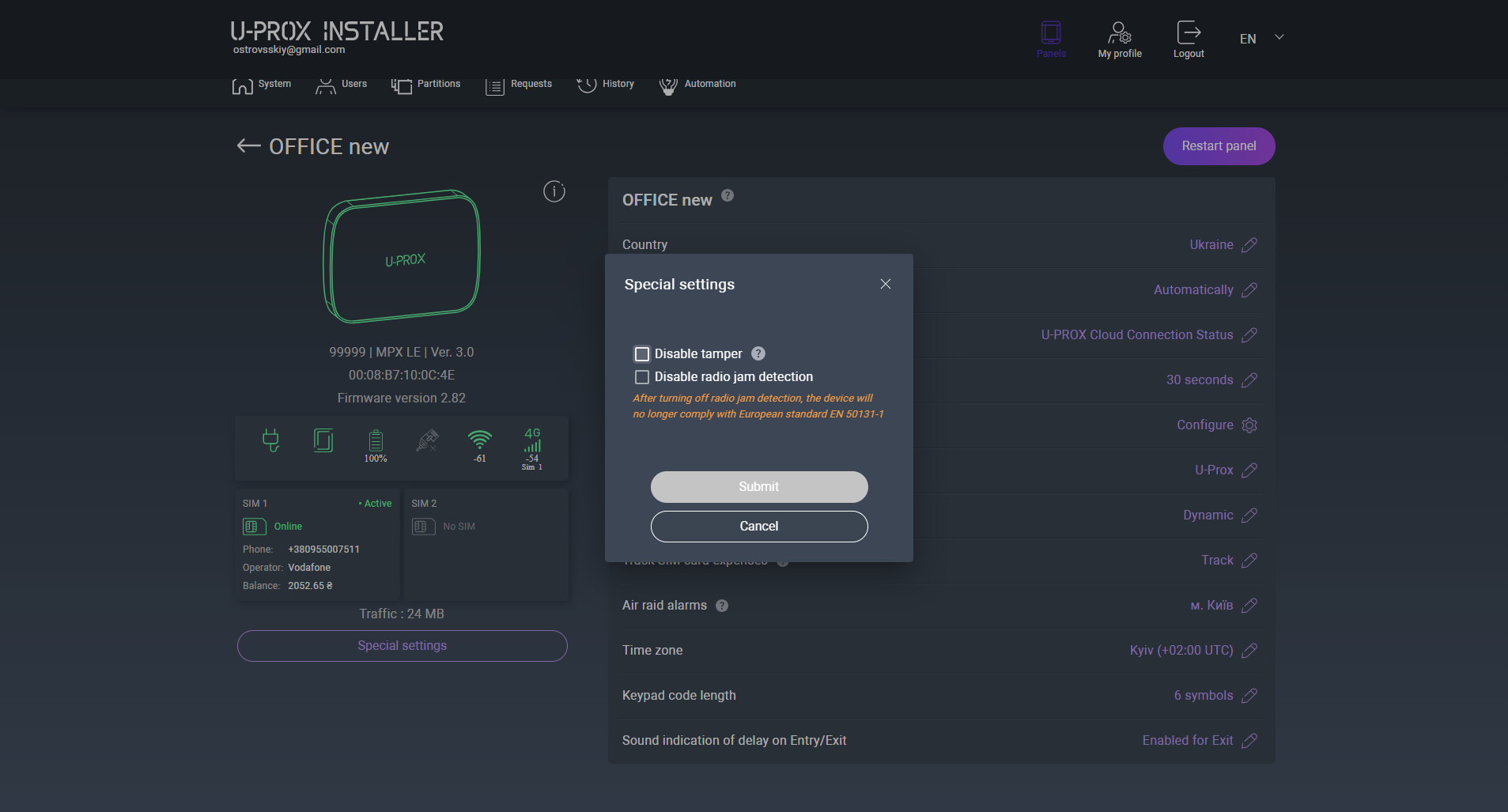
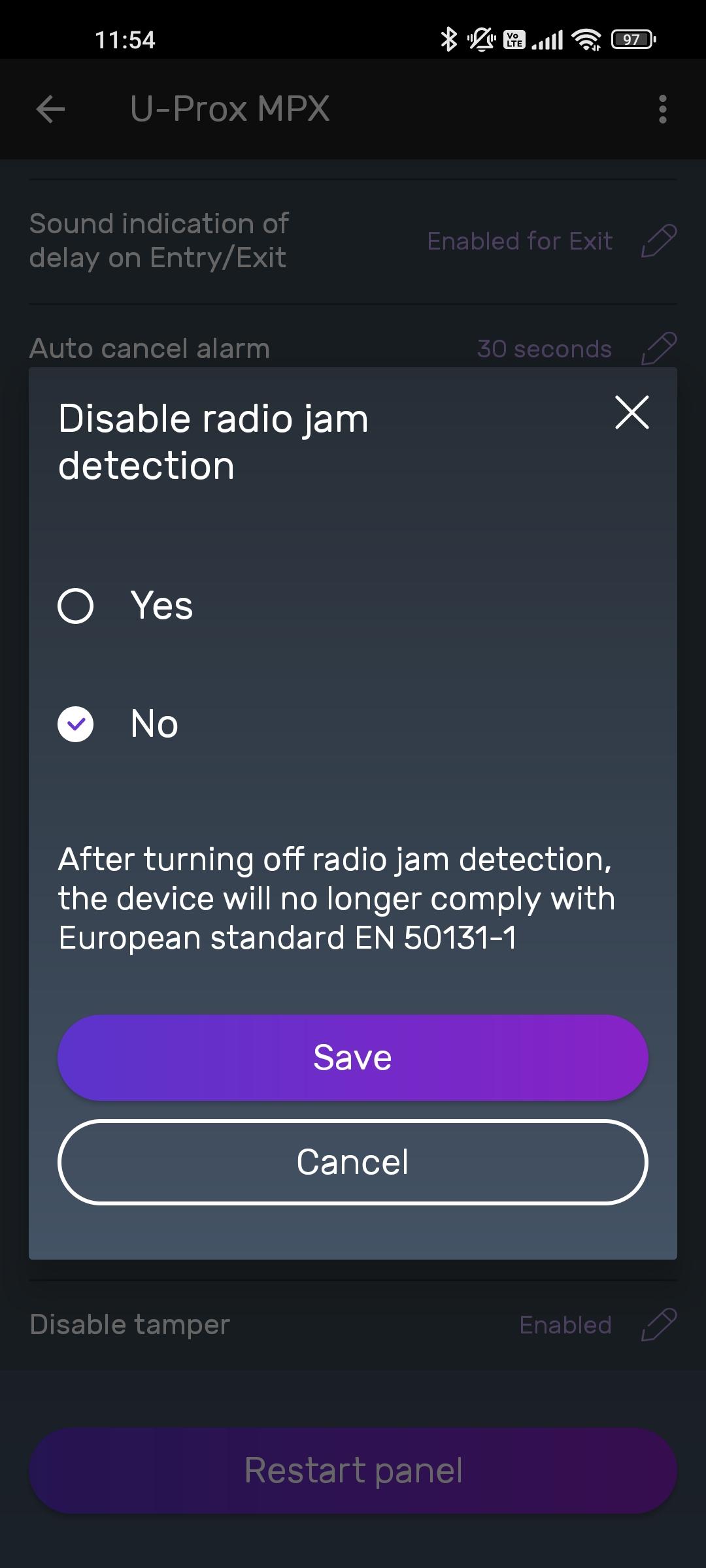
14. Special settings:
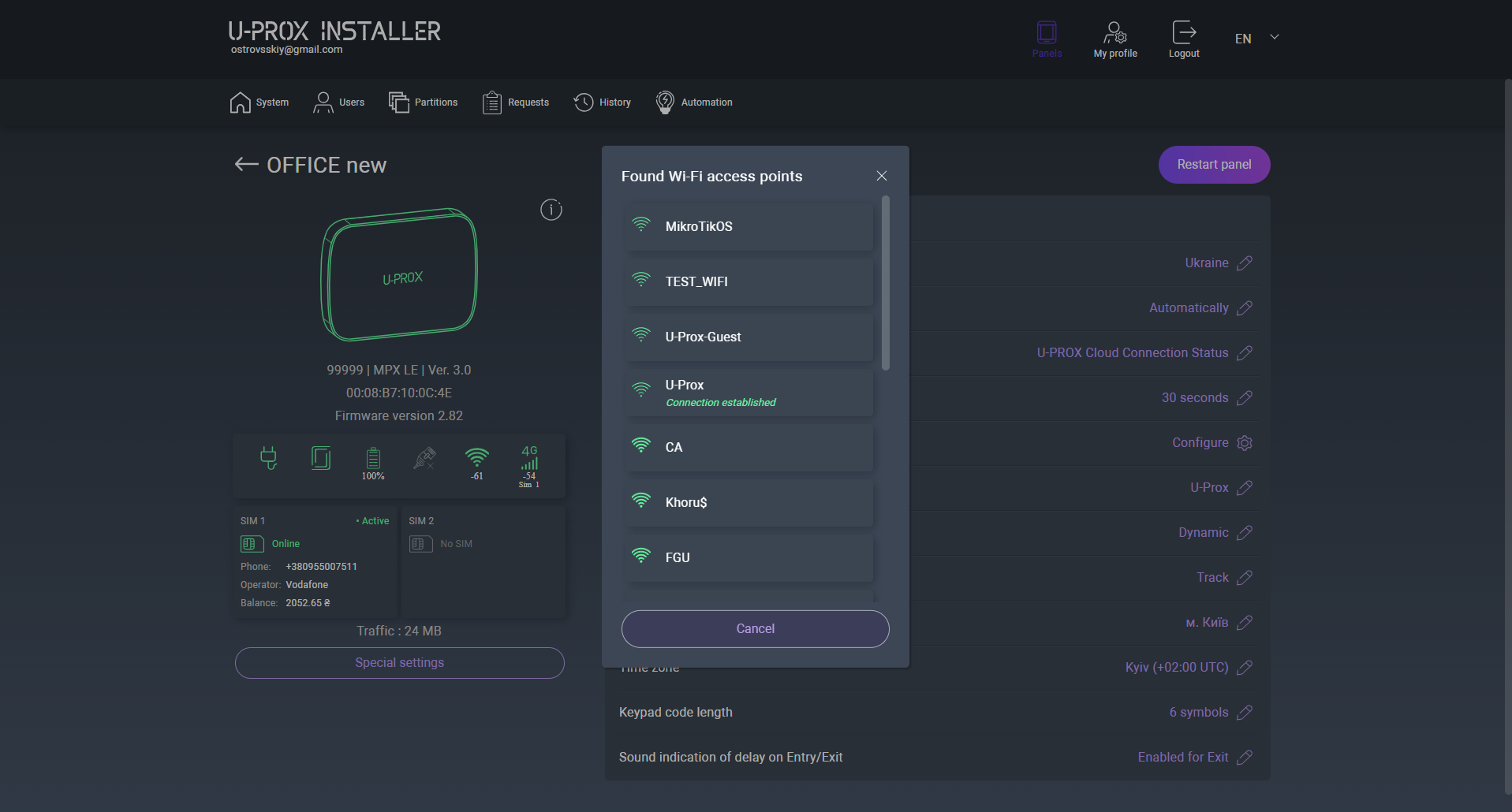
2. Go to the security control panel settings and select “Wi-Fi settings”
3. Press the “Search Wi-Fi access points” button
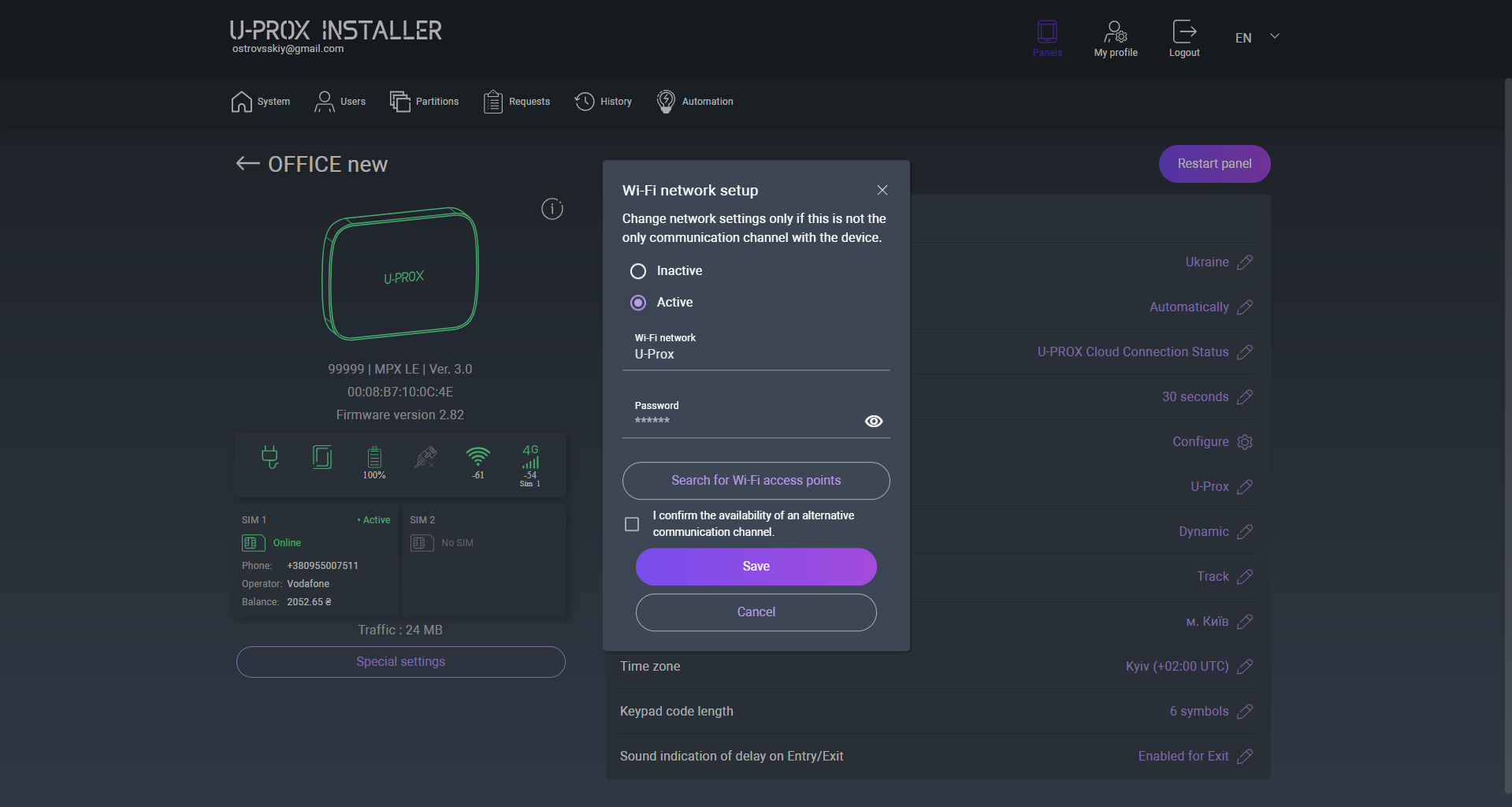
4. The following will be searched
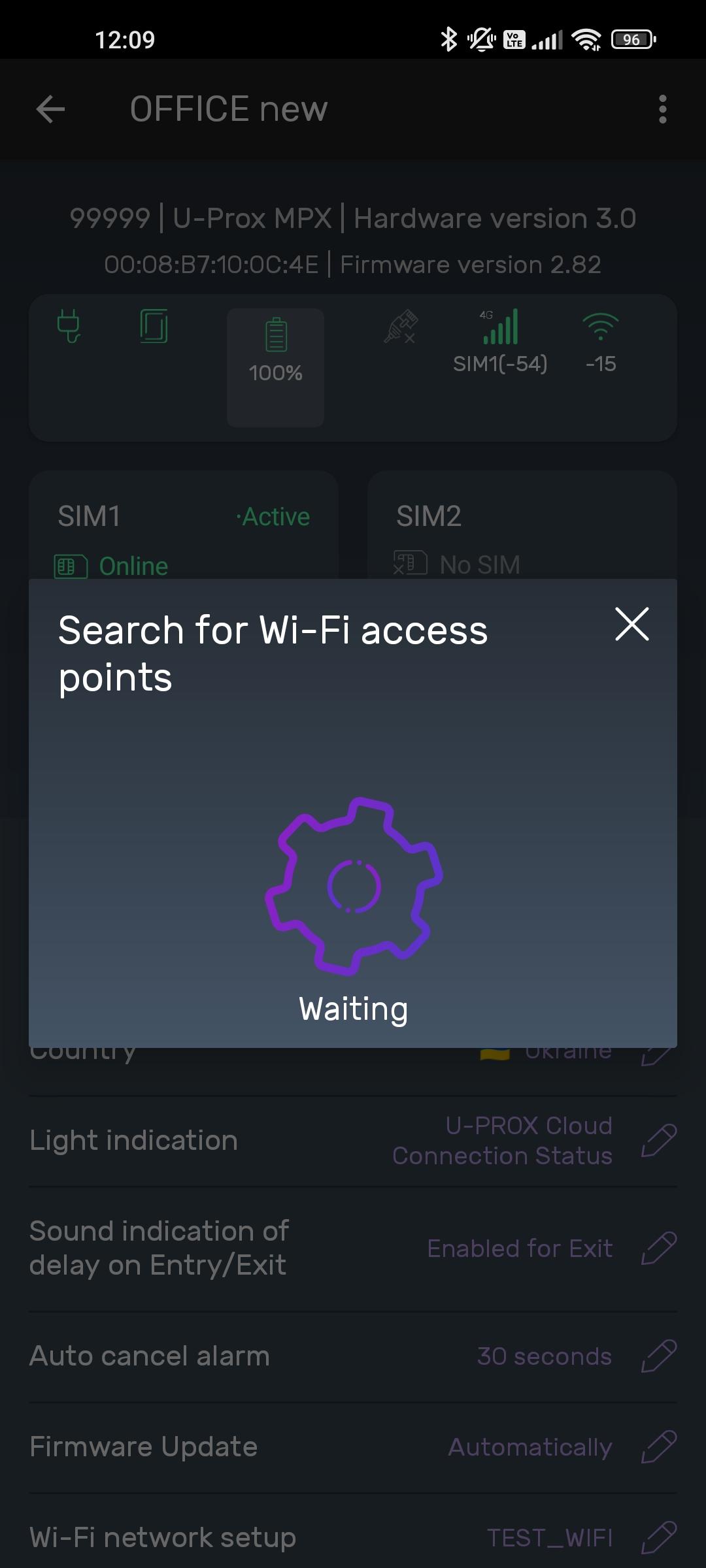
WARNING: THE DEVICE OPERATES ONLY WITH WI-FI 2.4 GHz. OTHER TYPES ARE NOT SUPPORTED AND WILL NOT BE DISPLAYED DURING SCANNING.
5. The found access points are displayed in the list. Select the network you want to
connect to from the list
6. Enter the password and confirm the availability of an alternative communication
channel in case the Wi-Fi connection fails
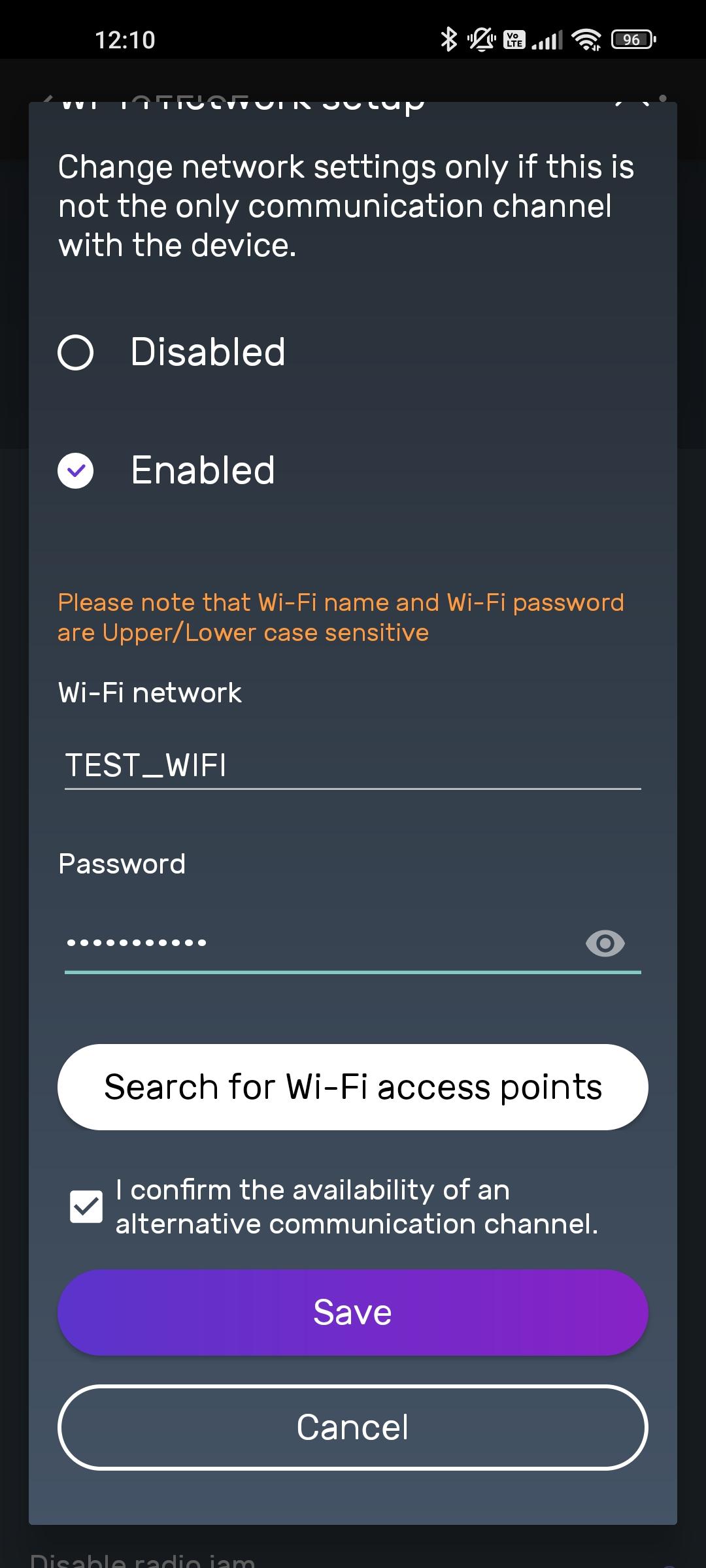
7. The Wi-Fi network will be connected
2. Select the SIM card for which special settings must be specified
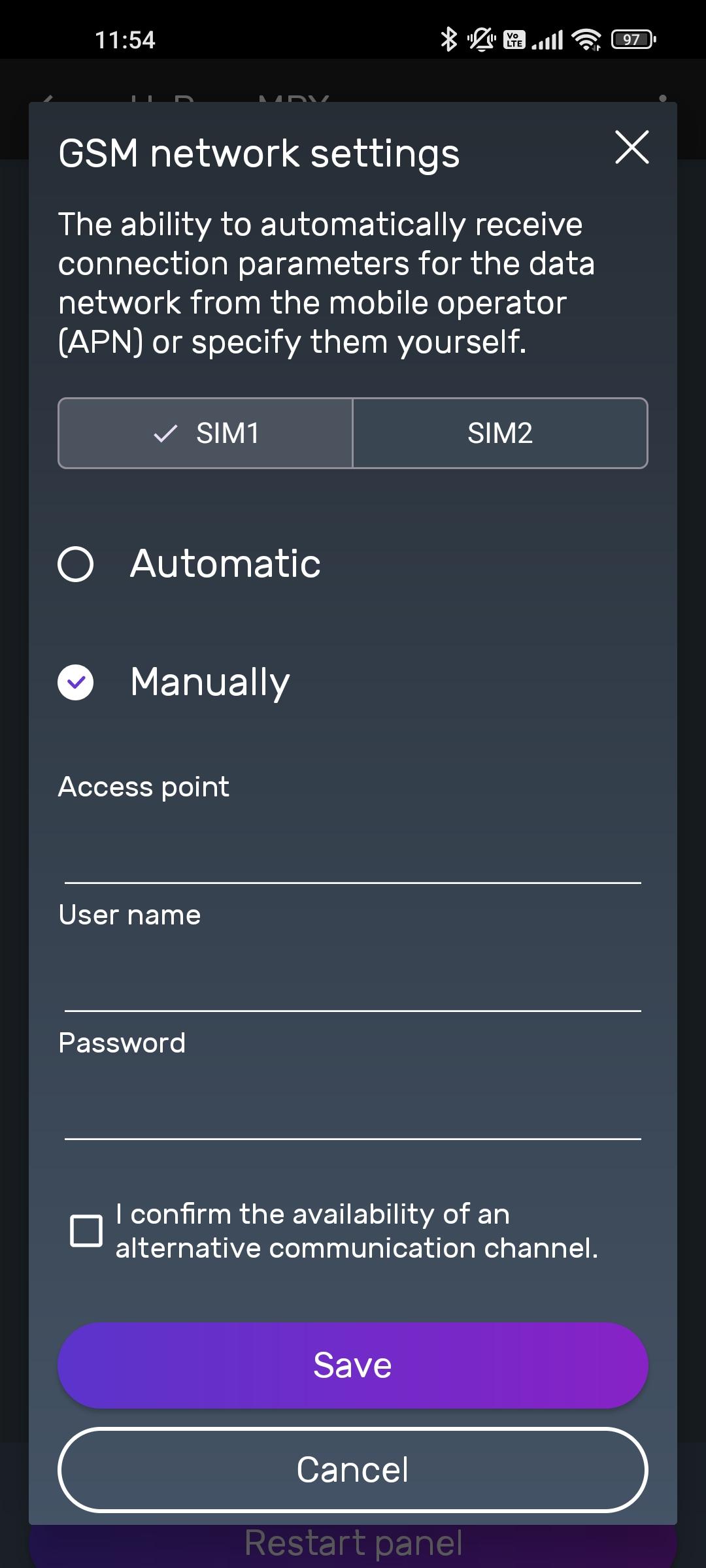
3. Set the required settings, confirm the presence of an alternative communication channel in case the connection is unsuccessful. Press the “Save” button
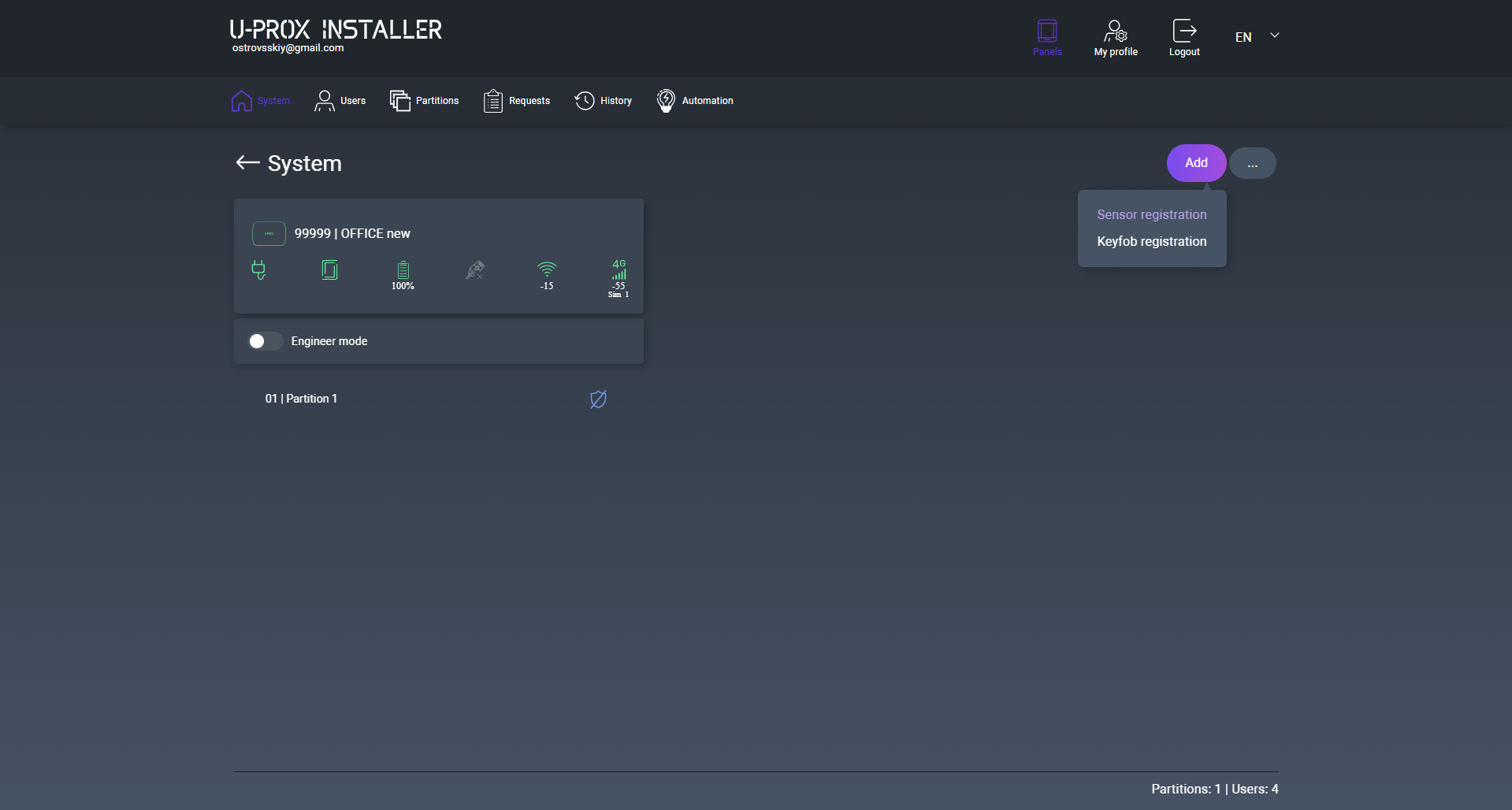
2. Press the (+) button (“Add radio devices”), the control panel will switch to the registration mode for detectors, keypads, etc. In this window, you can tap the device icons and view the activation instructions.
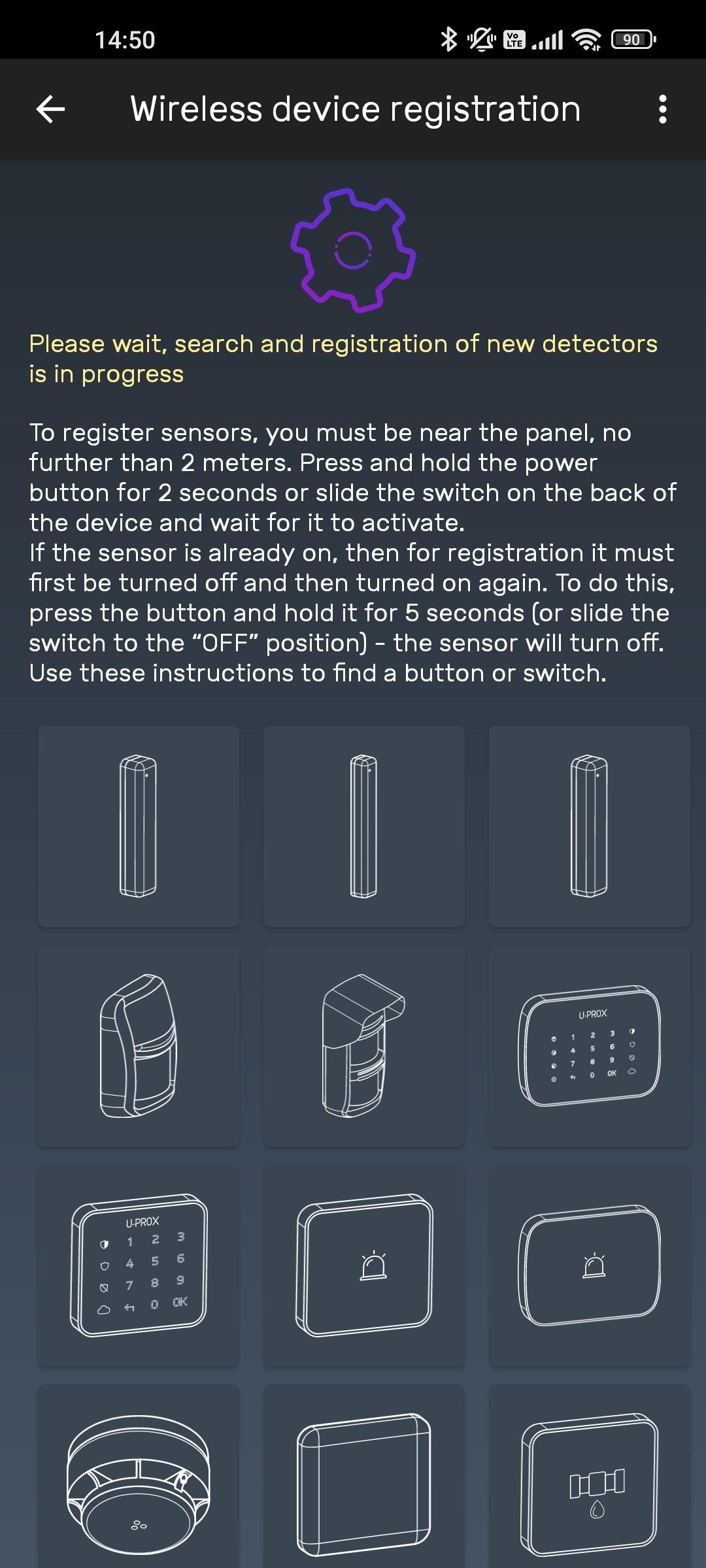
3. According to the instructions, turn on the wireless detector and bring it close to the control panel at a distance of approximately 1 meter
4. Wait 15–20 seconds – the wireless detector will be registered and its settings will open in the application
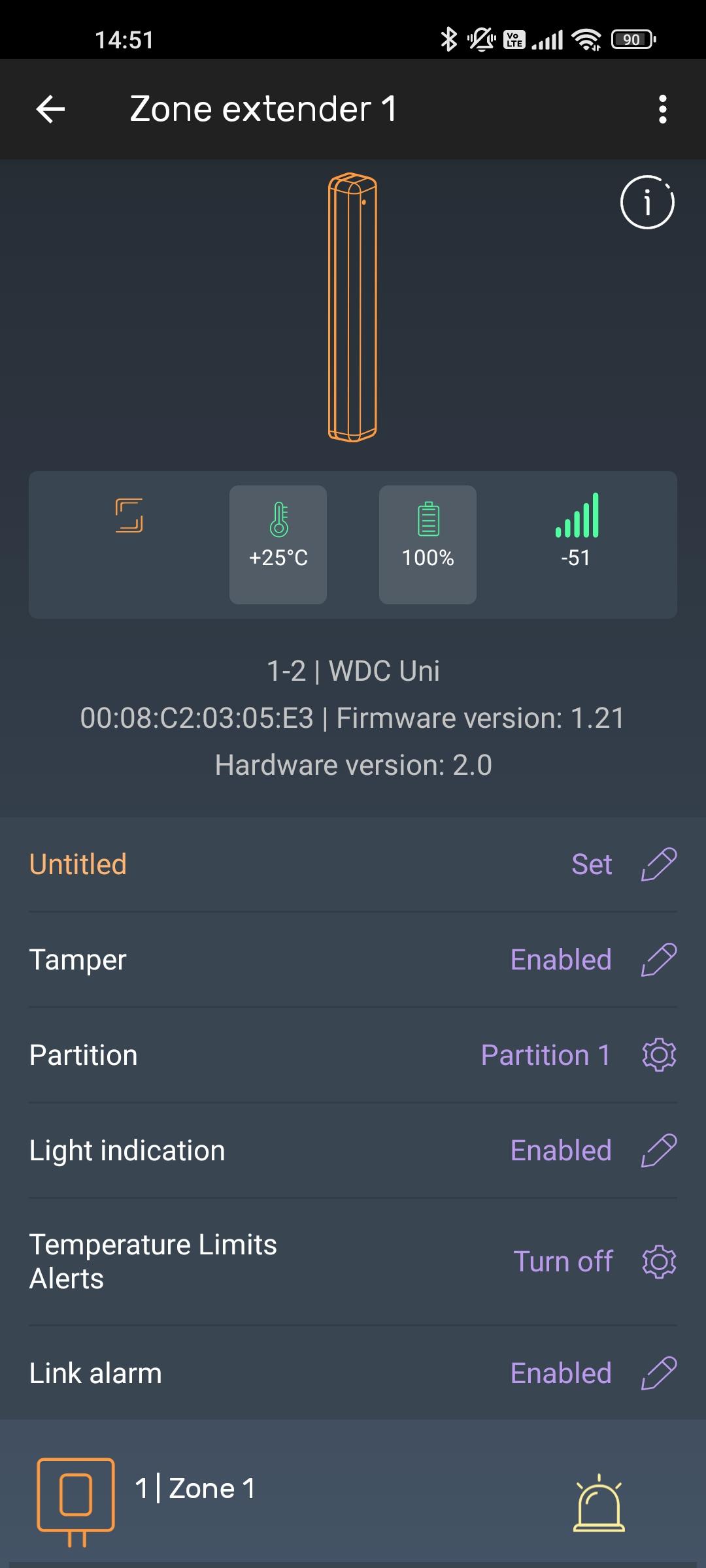
5. After changing the settings, device registration will continue
6. To complete registration, press the “Back” button in the application window

2. Press the (+) button (“Add user”) and enter their name.
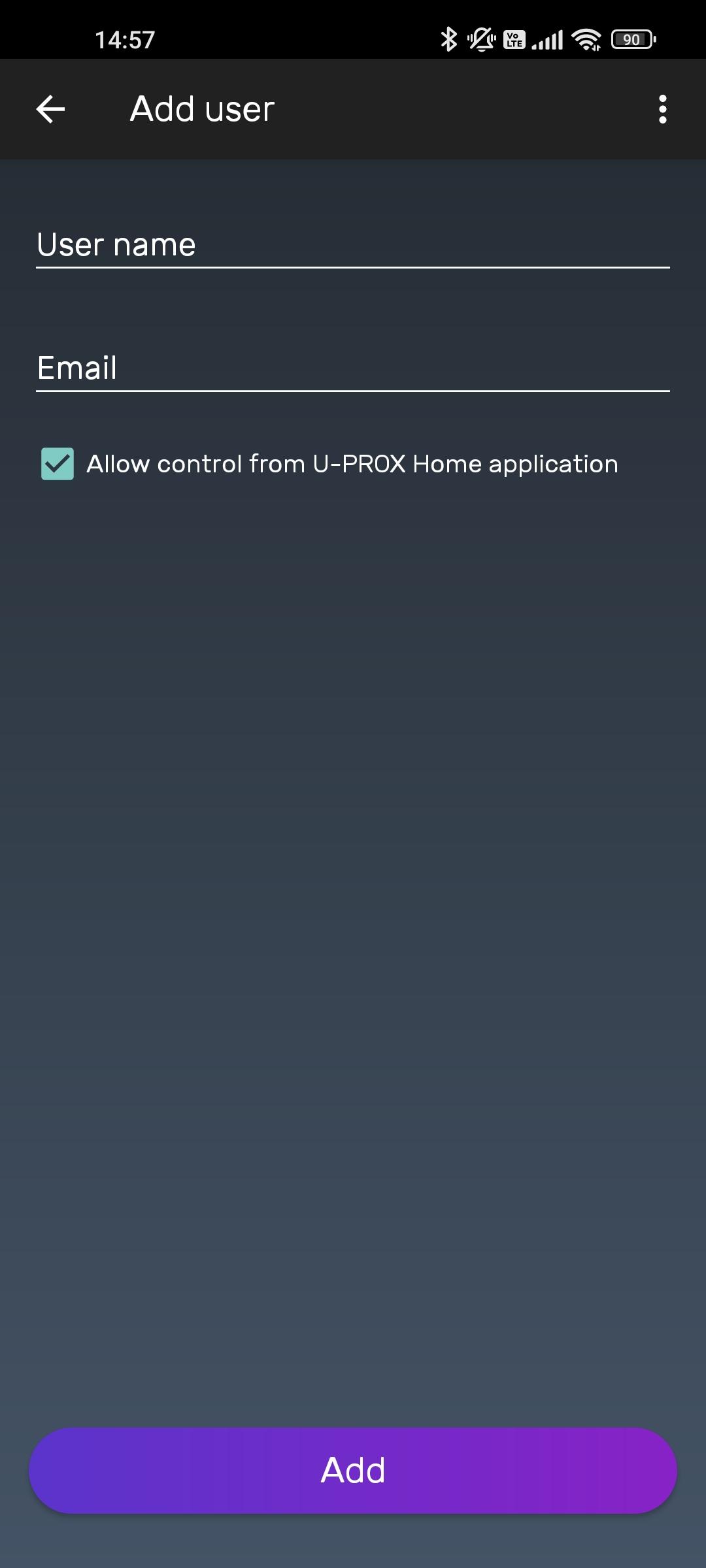
3. Press the “Add” button – the user will be created
If a keypad is used in the system, provide users with a PIN code.
2. Select a user from the list
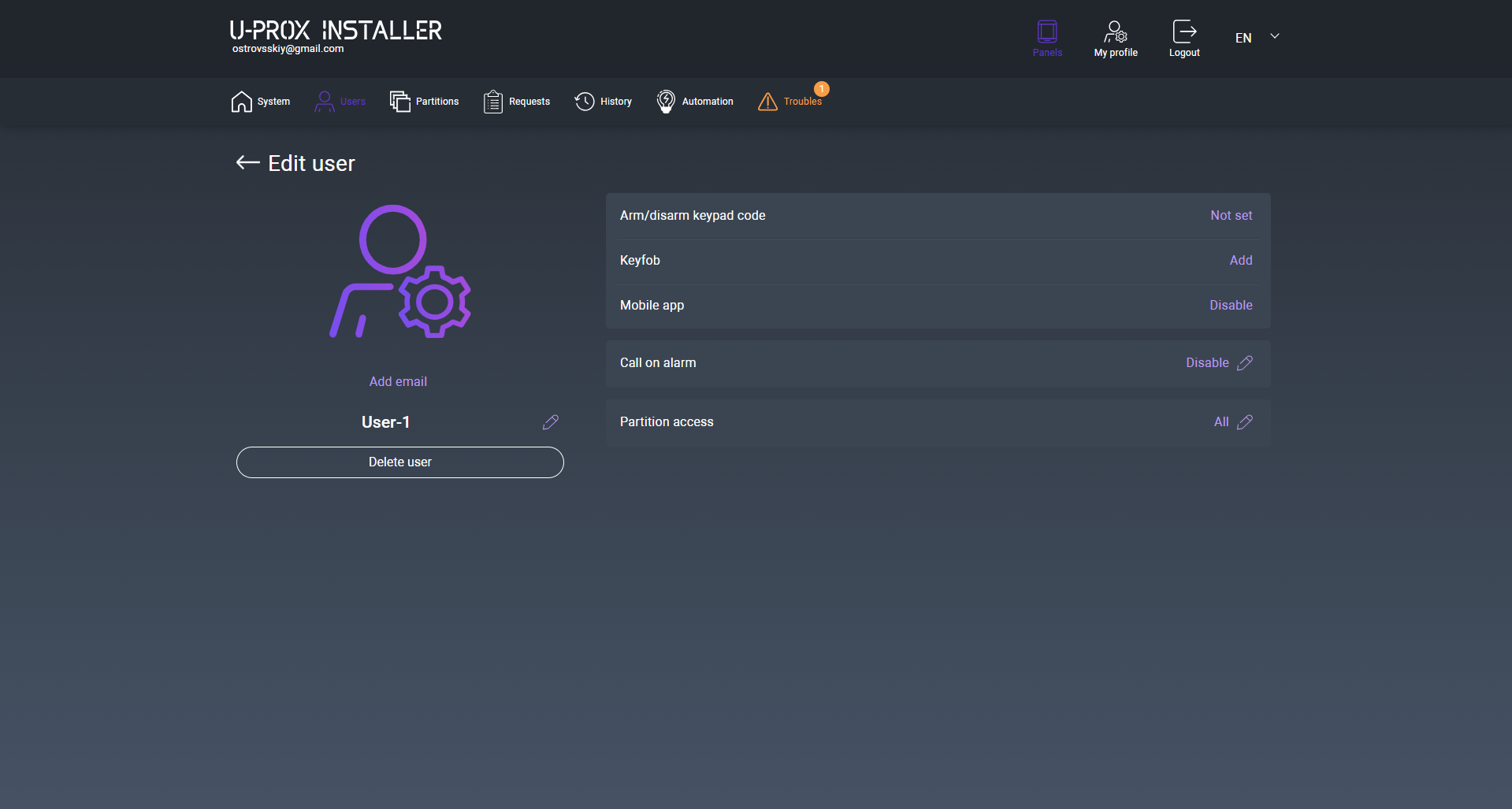
3. Select “Keypad code for arming/disarming”
4. Enter the keypad code and click the “Save” button
5. The passcode will be saved
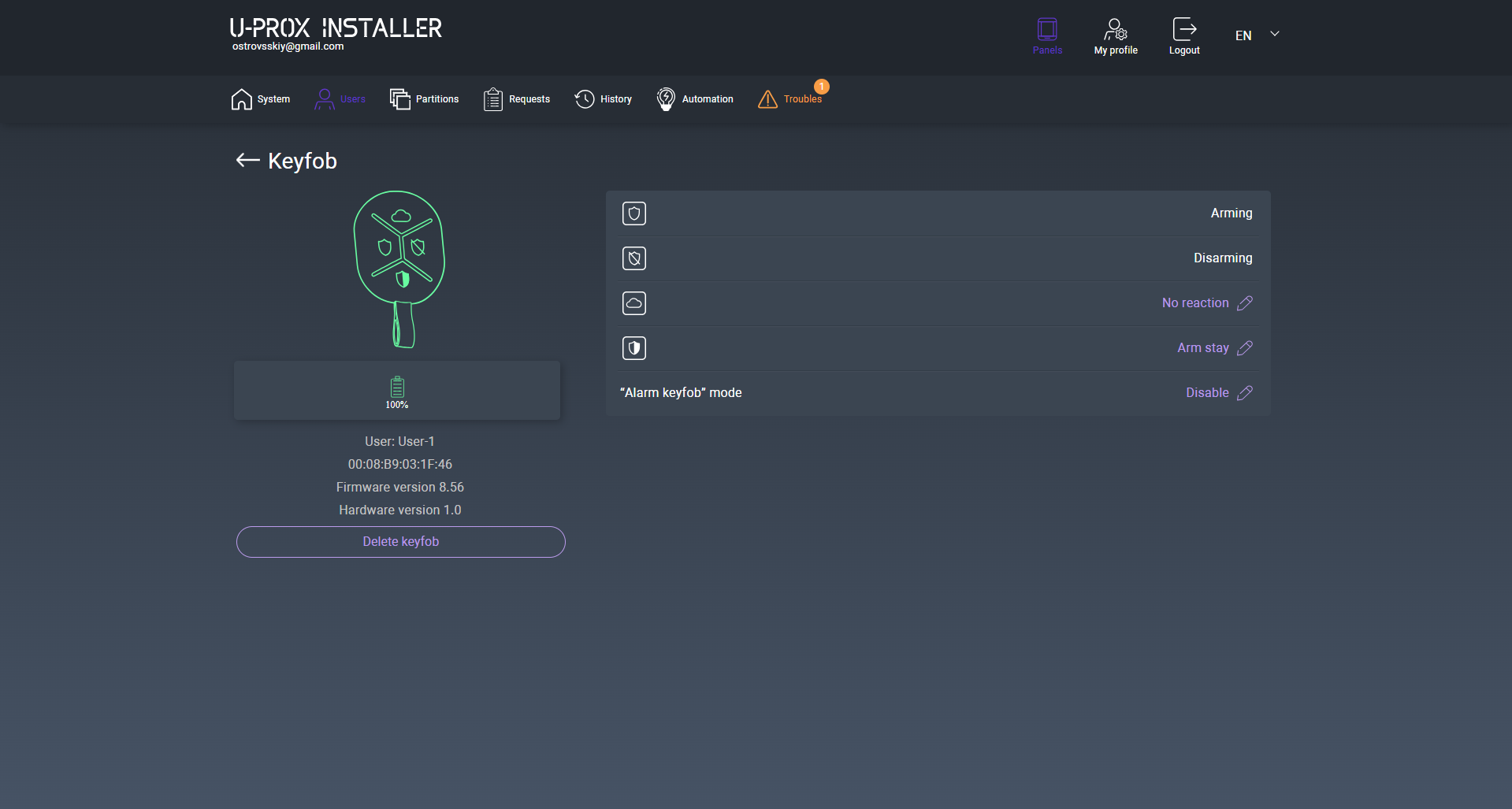
To add a wireless key fob to a user, perform the following actions:
2. Select a user from the list
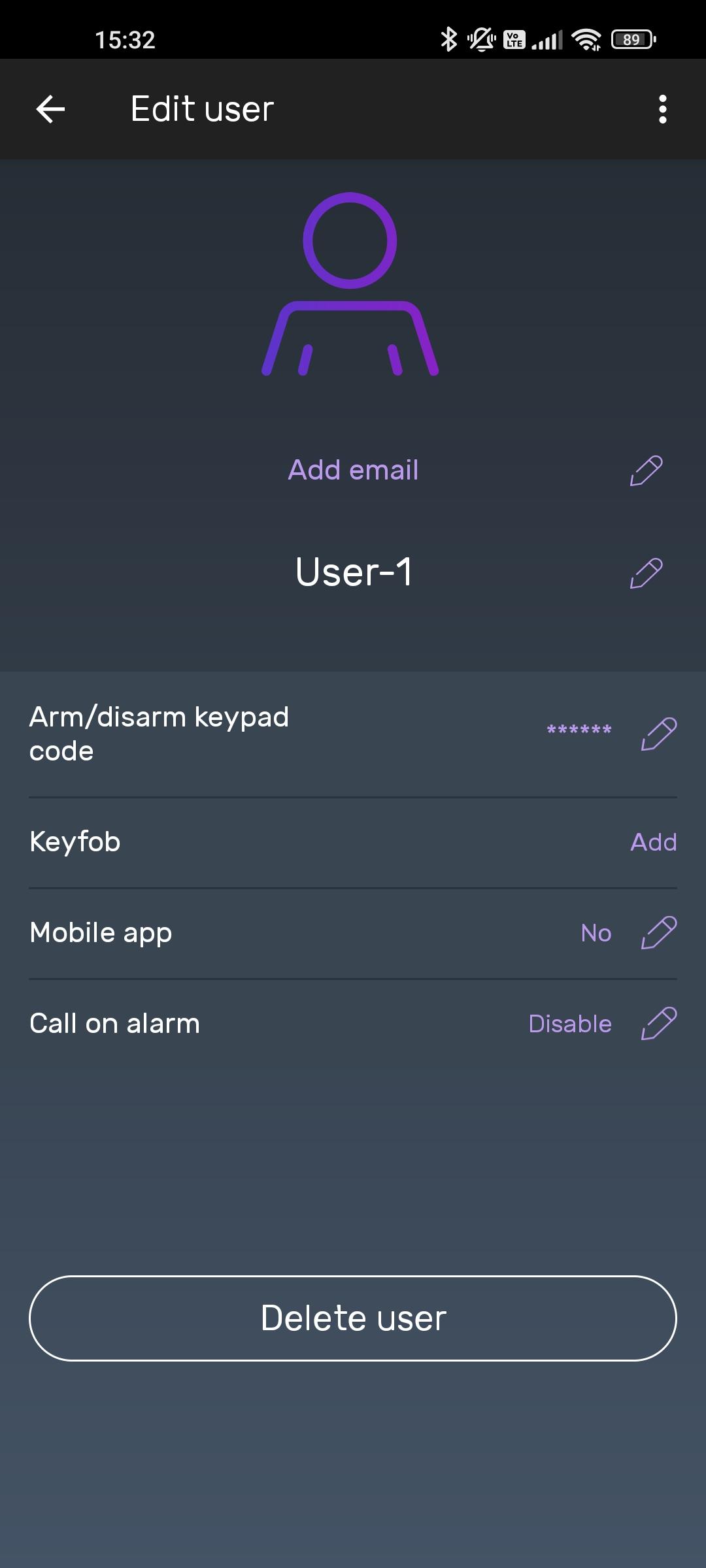
3. Select the “Key fob” item, key fob registration will be started
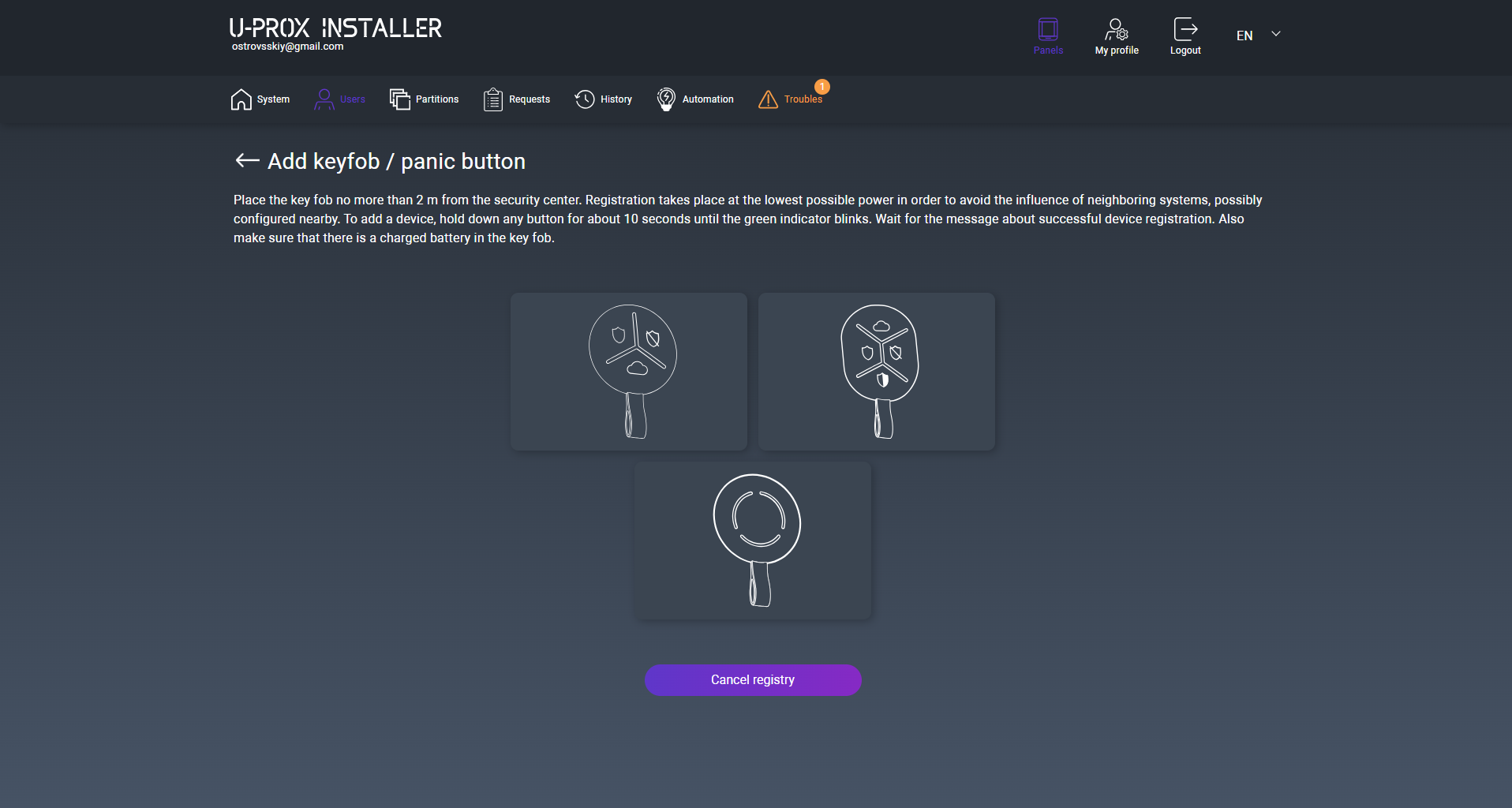
4. Bring the key fob to a distance of 0.5 m from the control panel, press and hold the button for about 20 seconds – the key fob will be registered. Release the key fob button.
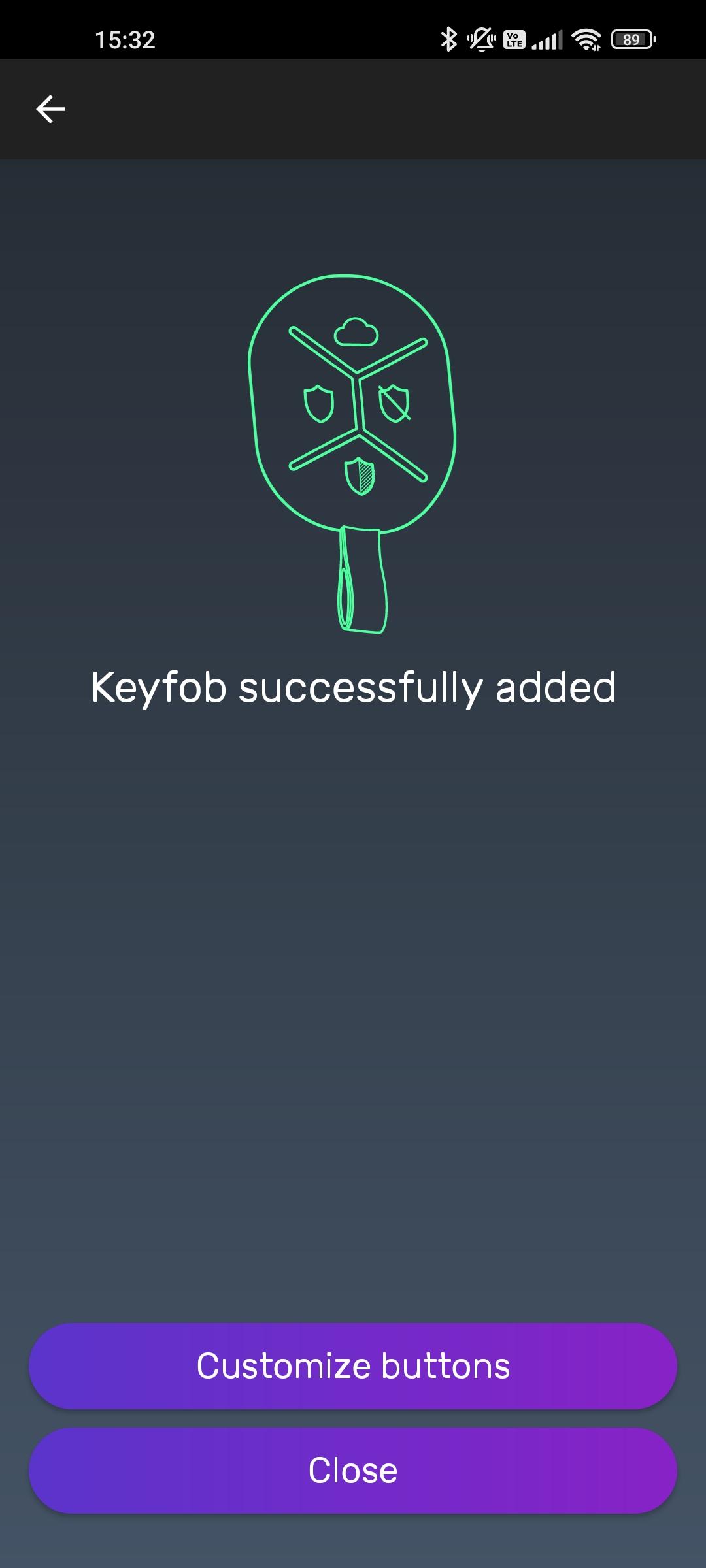
5. If necessary, press the “Change buttons” button to reconfigure the functions of the key fob buttons
2. Select a user from the list
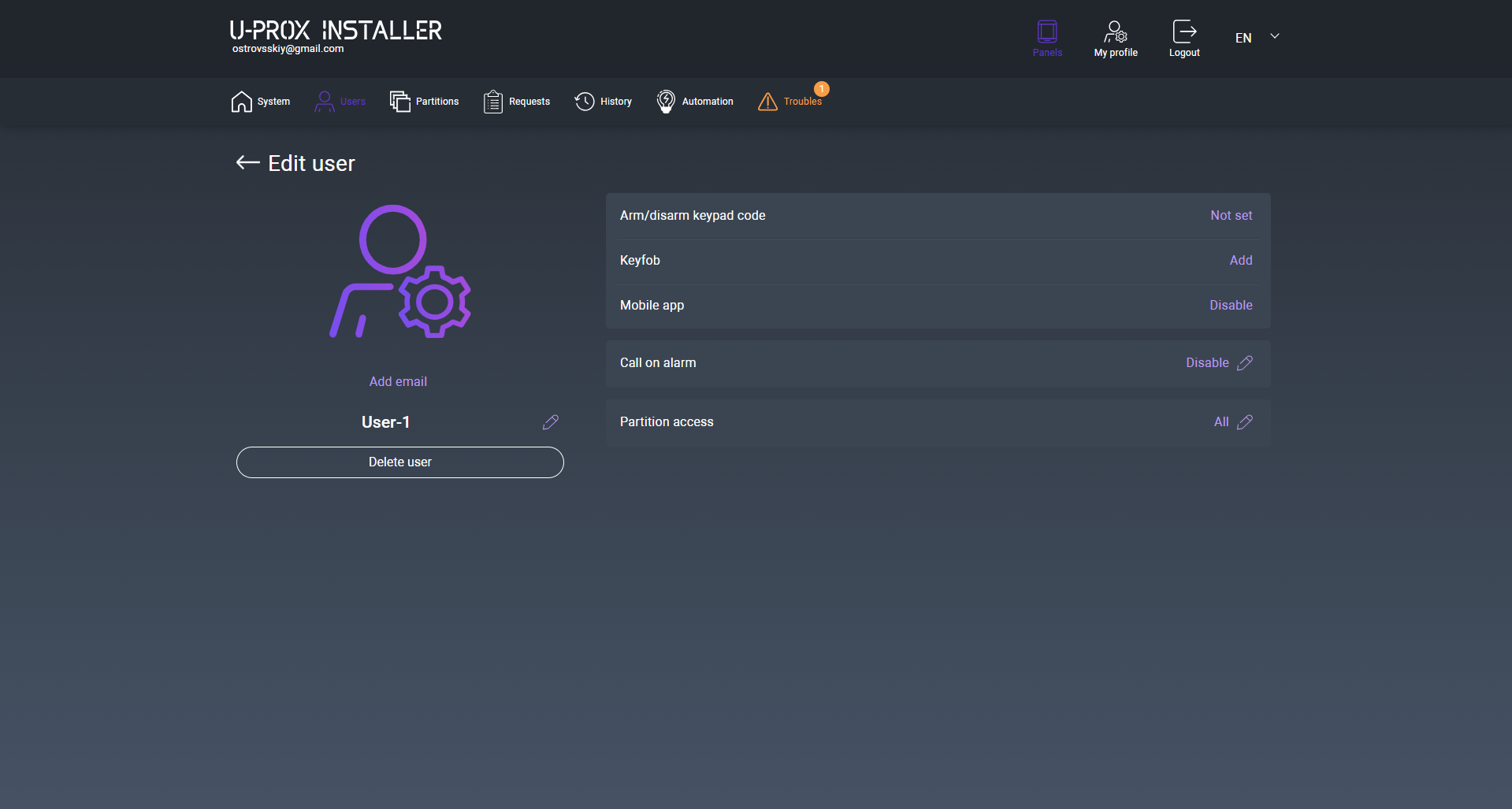
3. Select the “Mobile application” item
4. Specify the user’s e-mail address, select the “Allow” option and press the “Save” button
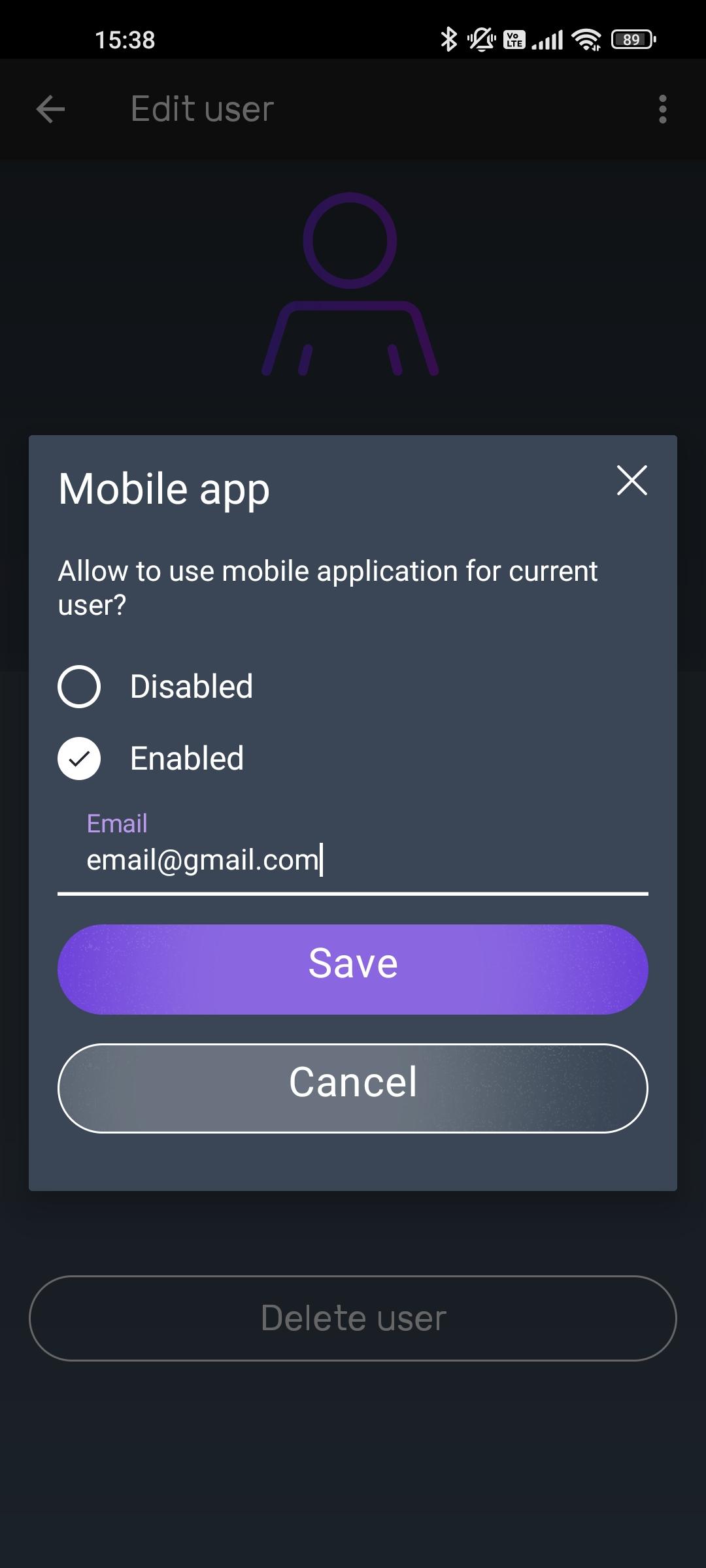
5. The user will receive an email with an access invitation to the specified e-mail address. If the application has not been installed before, the application will be downloaded and installed. After launching the application, if necessary, a new user
will be registered.
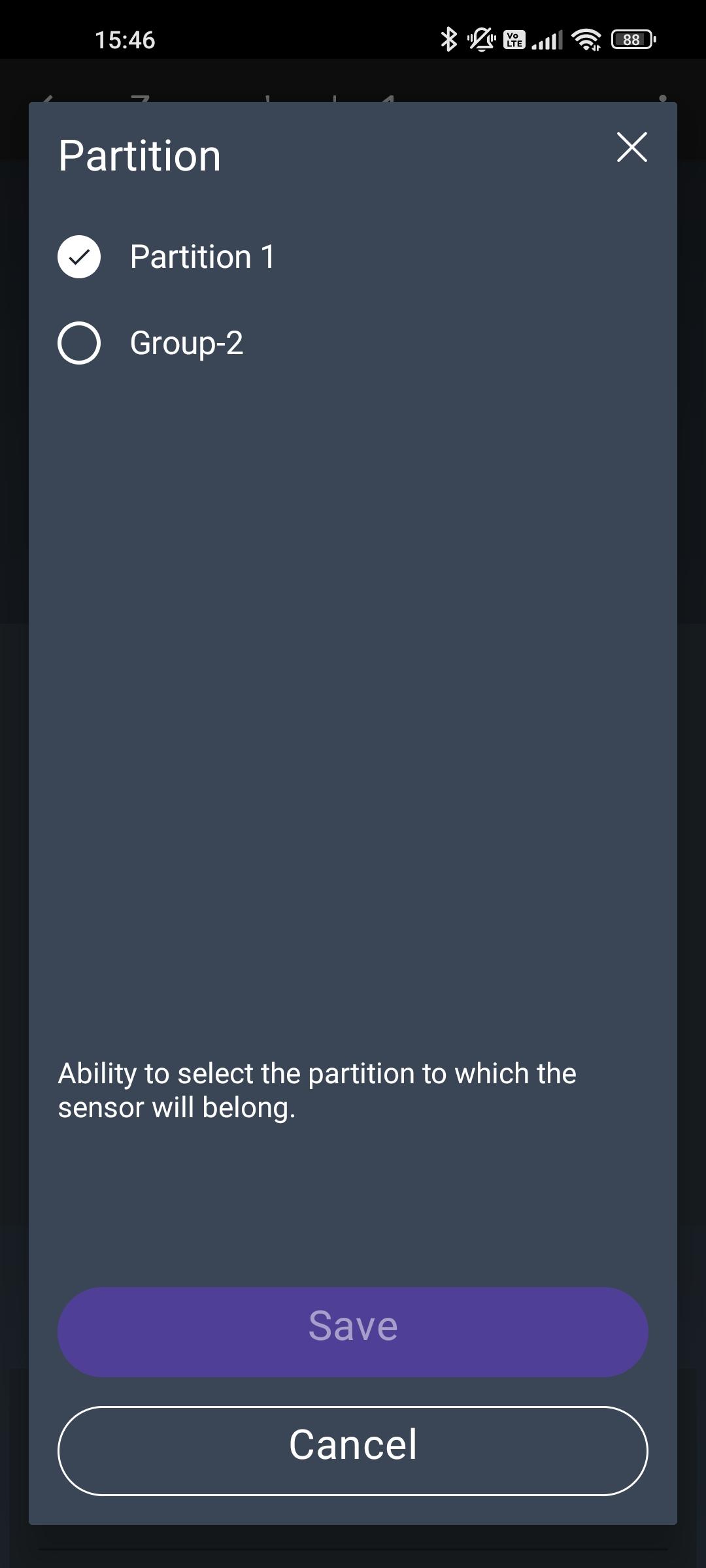
A security group is a logical combination of protected premises zones (for example, a room, apartment, garage, floor of a building, etc.), the minimum unit of protection. A security group allows you to control all zones simultaneously. Security groups are independent – the user can manage and see only those security groups, devices, and events within them to which access has been granted.

2. Press the (+) button (“Add group”), enter the group name and press “Save”
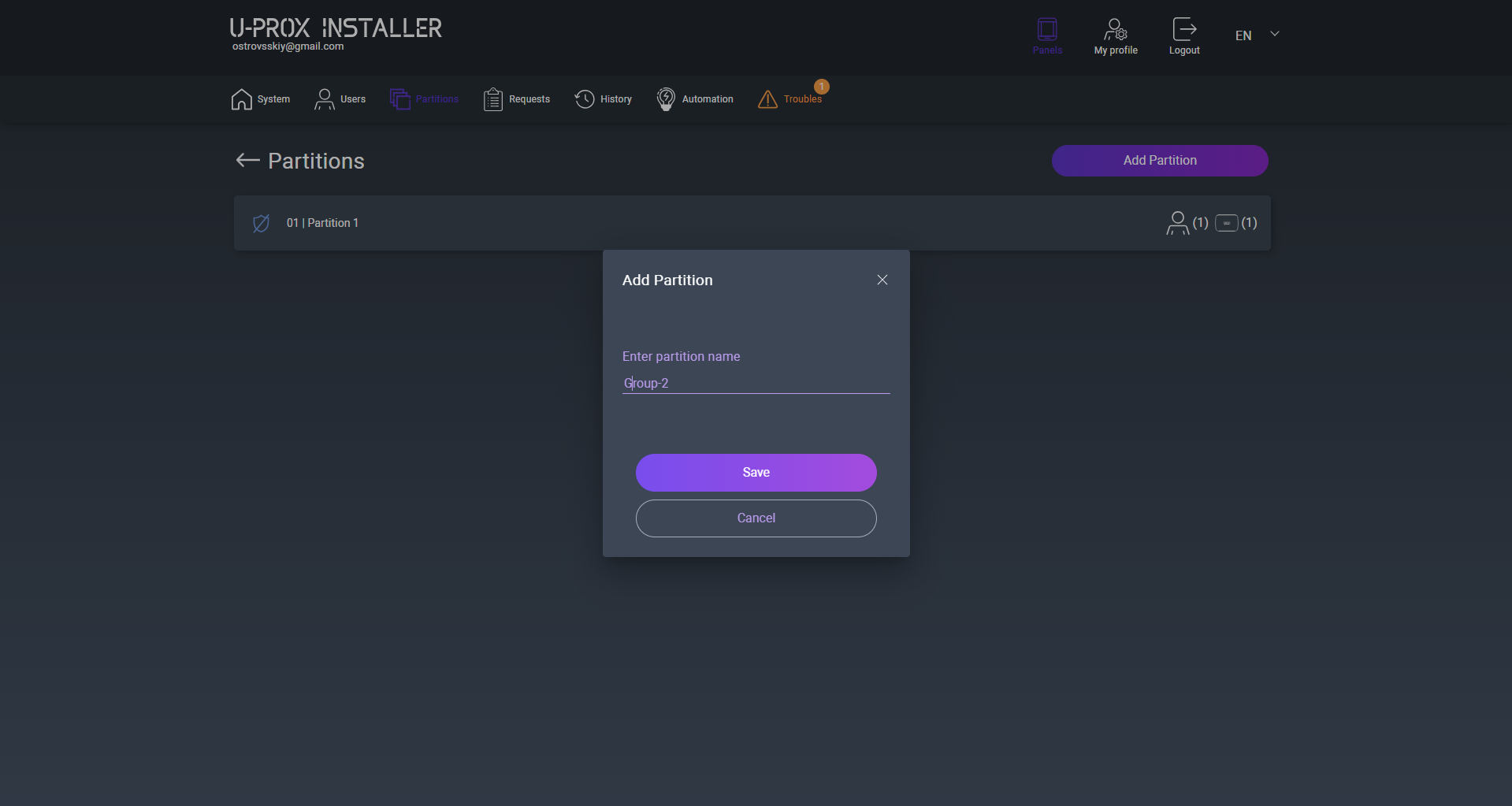
3. In the detector properties, you will be able to assign the detector to another group
Connecting the system to a security company allows you to receive round-the-clock monitoring of the security system status, rapid response to alarms with the involvement of rapid response teams and engineers to maintain the equipment.
Each security system is identified by the security company by an internal identifier – a monitoring station number or account.
2. Go to the “Remote control” section
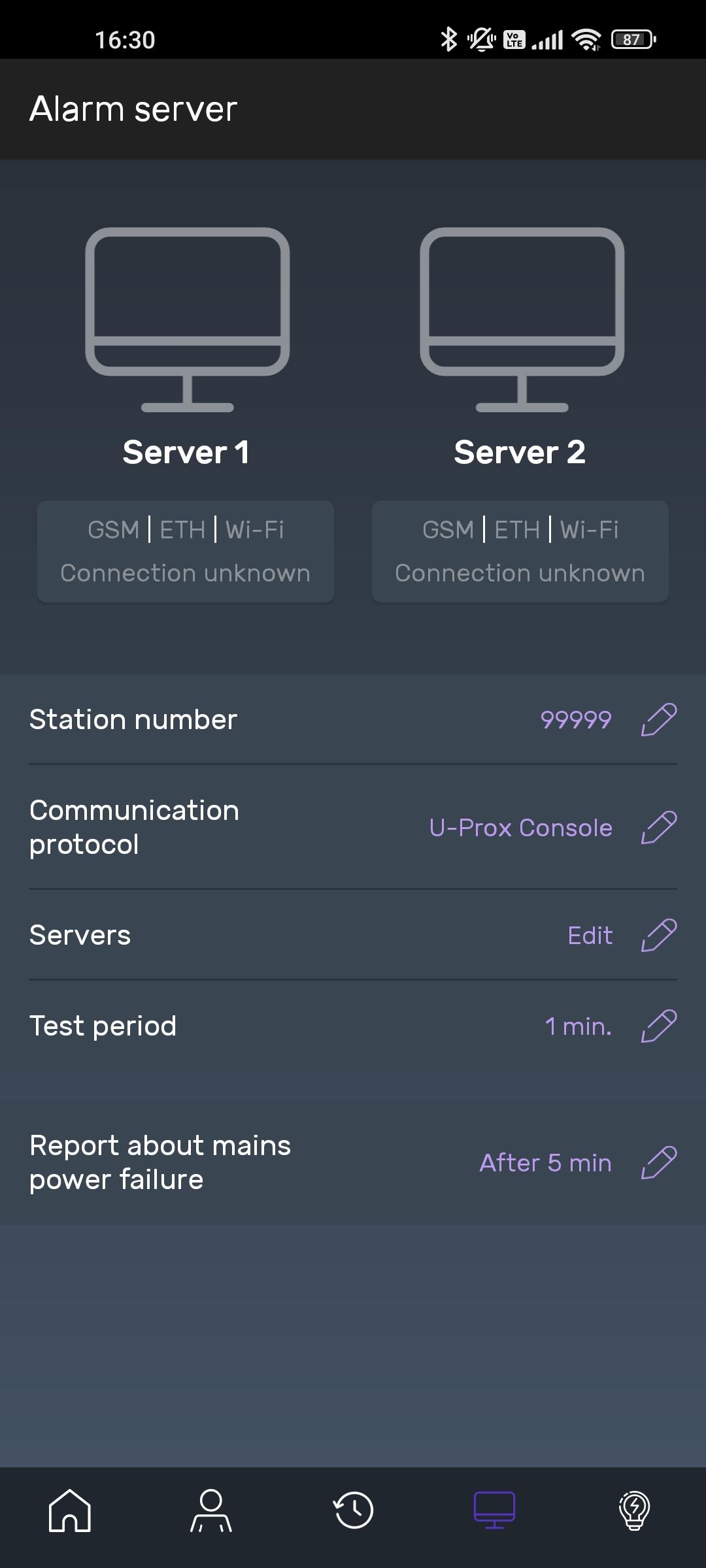
3. To connect to a security company and work through the cloud, it is enough to set only the monitoring station number of the security system
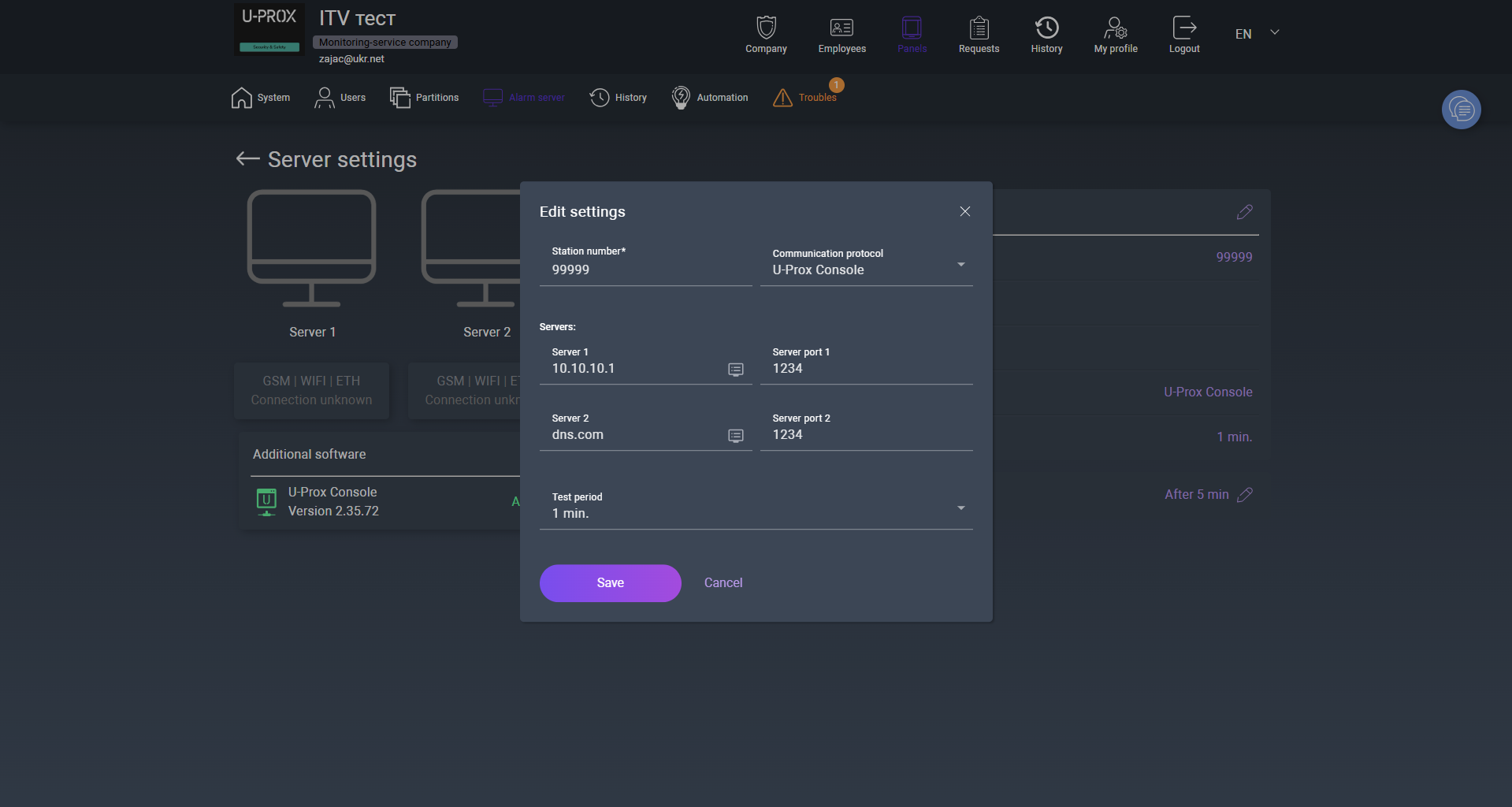
4. To connect to a security company and operate directly with backup via the cloud, it is necessary to set the control panel number of the security system and specify the IP address and port of the event receiver
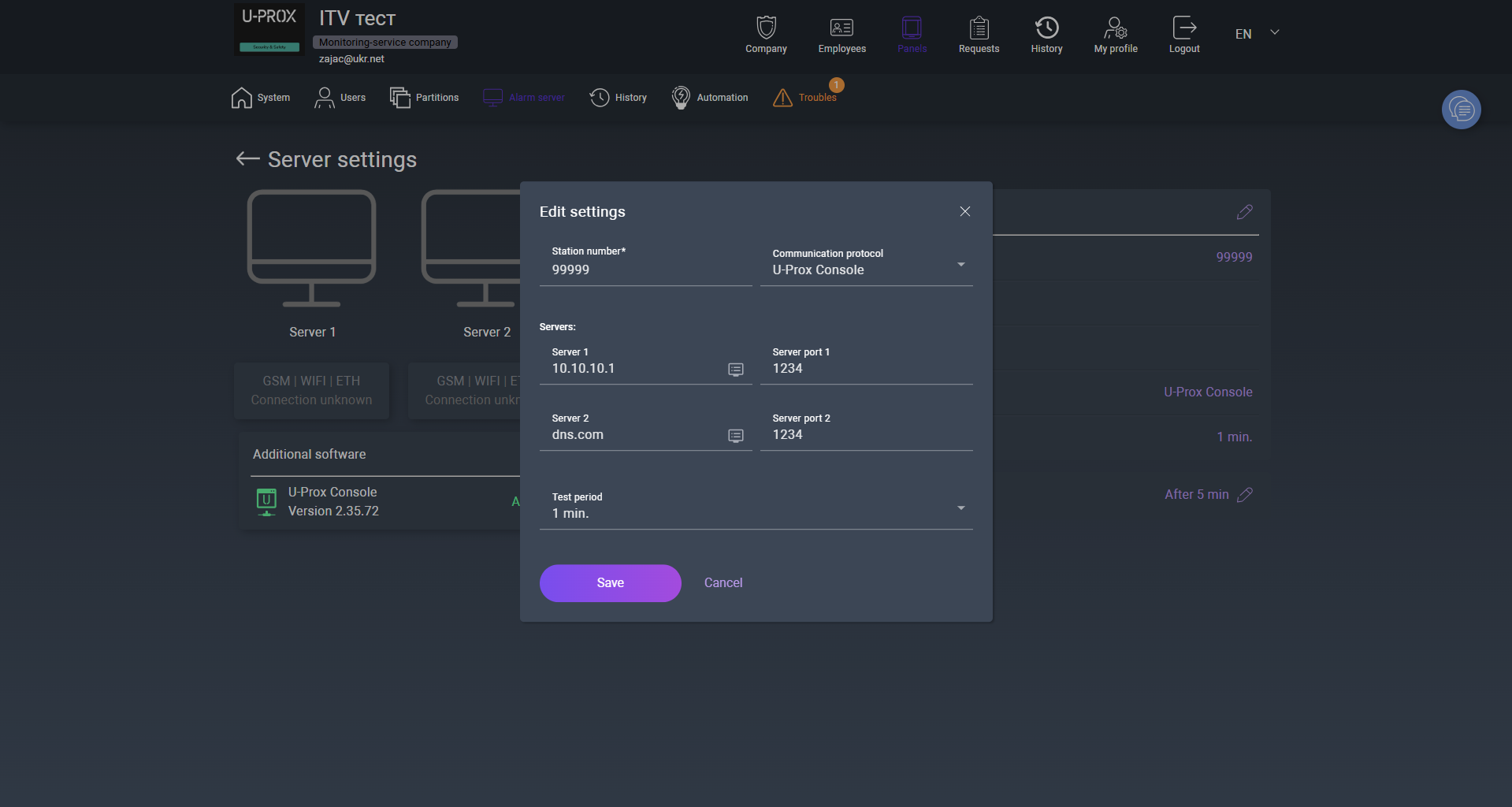
5. Additionally, a test period is configured – the time interval for sending the “Periodic test” notification, which is used to monitor the status of the device and the communication channel between the device and the security event receiver.
2. Select the deletion method – full, with clearing all settings (the “Clear all settings…” option is enabled, the device must be online), or partial – the device will be disconnected from the account, but all settings will be preserved (the “Clear all settings…” option is disabled)
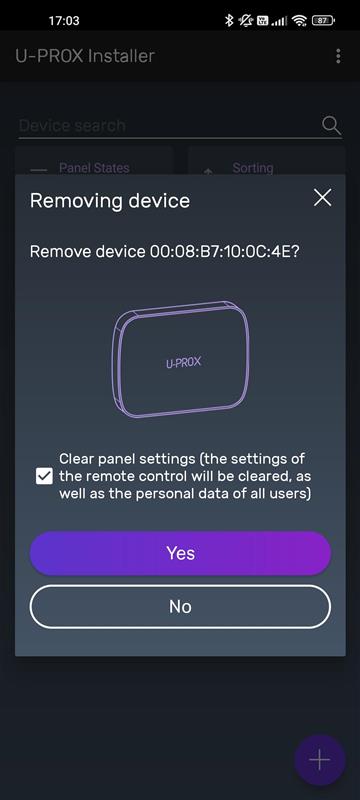
3.Press the “Remove” button to remove the device.
|
main power is OK |
|
|
main power is absent |
|
|
device enclosure is closed |
|
|
device enclosure is open |
|
|
battery is charged |
|
|
battery charge level |
|
|
battery is critically discharged |
|
|
battery malfunction |
|
|
Ethernet communicator is OK, connection to U-PROX Cloud is available |
|
|
no connection to U-PROX Cloud |
|
|
no Ethernet connection |
|
|
connected via Wi-Fi, signal levels |
|
|
Wi-Fi connection is absent |
|
|
mobile Internet, 2G connection, signal levels and active SIM card number |
|
no 2G connection |
|
|
mobile Internet, 4G (LTE) connection, signal levels and active SIM card number |
|
|
no 4G (LTE) connection |
|
220V power supply is normal |
|
|
220V power supply not available |
|
|
device temperature sensor |
|
|
device housing closed |
|
|
device housing open |
|
|
battery charged |
|
|
battery charge level |
|
|
battery critically low |
|
|
battery is faulty |
|
|
level of radio communication with the device |
|
|
No radio connection with the device |
|
|
passage (bypass) of the zone during the security period |
|
|
sensor tilted or inverted |
All critical events (alarm, loss of communication, low battery, tamper triggering) are displayed in the application in real time and are accompanied by push notifications.
The event history allows viewing all actions and system states for the selected time period.
Depending on the granted rights, the user can manage security groups, devices, and automation elements.
Changes to system settings are logged and available for review in the event history.
3. During the first installation, the application will request additional settings, such as a security PIN code, geo-reminder settings, application appearance, and, if the appropriate right is granted, additional settings when using the panic button


4.The main screen of the application can have two views: one group and horizontal navigation through the groups in a slider (view A) and a view with a list of groups (view B)

At the bottom of the screen there is a navigation panel that provides movement to the main functions: Security,Settings, Automation, Cameras, Events.



Sending the “Attack” (“Panic” or “Silent alarm”) signal. This function must be enabled in the user properties.

To cancel the alarm, it is enough to disarm the group, or press the “Arm” and immediately “Disarm” buttons
3. After successful download of the module, press the (+) button to add a camera, and select its type from the menu that appears
4. When adding a Dahua/Imou camera, it is enough to set the camera name and read the serial number using the built-in QR code scanner.
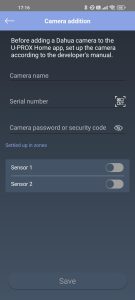
5. Specify which security zone the camera is linked to, so that in case of an alarm in the zone the video from the nearest camera is displayed, and press “Save”. For verification, you can view the video
6. In order to add an RTSP camera, specify its name and the rtsp link
2. To filter events by types, use the “Filter” button
This menu contains additional parameters for configuration and control of the security system
2. “Sensors and key fobs” – information about devices in the system and their status. Also provides the ability to view statistics on temperature changes and battery discharge. From this menu you can disable (skip or “bypass”) a faulty sensor.

3. “Users” – view system users and, if the appropriate right is granted, edit them
4. “Notifications and reminders” – configuration of notifications and reminders about arming and disarming according to geolocation
5. “Application appearance” – configuration of the appearance of the main screen and sensors for displaying temperature on the main screen

6. “Passwords and login” – additional security settings, such as biometric identification and an additional PIN code for logging in to the application
7. “About the application” – view the application version and send a request to the technical support service
Factory reset does not remove the device from the owner’s account or the security company account!
IF THE POWER BUTTON IS RELEASED DURING THE SERIES OF SOUND SIGNALS, THE DEVICE WILL NOT RETURN TO THE INITIAL SETTINGS.
The manufacturer guarantees that U-PROX MPX L meets the parameters described in this manual, provided proper storage and operation.
The manufacturer reserves the right to make design changes that do not affect key characteristics or reliability.
Training courses covering the installation and use of the U-PROX MPX L are conducted by “Limited Liability Company Integrated Technical Vision.” For additional information, please contact company employees using the phone numbers listed below.
Technical support:
https://t.me/u_prox_support_bot
This support is intended for trained specialists. End users should contact their dealers or installers before contacting “Limited Liability Company Integrated Technical Vision.”
Technical information is available at: www.u-prox.systems
Technical documentation
Photos of the devices
Photos for online stores
Declaration of conformity
CE certificate
Declaration of compliance with RoHS
Security Grade certificate
Full user manual
AU Cyber Security Rules Statement
Most of the sensors are powered by lithium batteries. They have sufficient capacity and operating temperature range.
Thanks to the adaptive power of the radio transmitters and the optimized data transmission protocol, the service life can be up to 7 years. The shortest service life of alkaline batteries “finger” or AAA, which are installed in the keyboard – up to 2 years.
But the replacement does not even require a screwdriver, the keyboard is removed using a regular plastic discount or bank card.
Everything that is in U-PROX, from the idea to the engineering implementation is done exclusively in Ukraine.
15 years ago massively used wired phones, mobile phones were either business or luxury. Now almost everyone has a mobile phone. It’s not only comfortable. The quality of wireless communication is steadily increasing.
The same situation with security systems. Wired systems require high-quality cable, trained personnel with electrical education, quality installation with line inspection, construction work with drilling, wiring, and other inconveniences. All this requires a lot of time.
As a result, we have a total cost that includes work. And compared with wireless systems, it is much higher. The wireless security system can be installed independently, the kit includes everything you need for installation.
The U-PROX security system has U-PROX BAND radio communication technology. It has unsurpassed characteristics in range, resistance to interference, due to channel redundancy, and is very efficient in terms of energy consumption.
It is reliable communication that distinguishes the U-PROX security system from its competitors. We use DSTU GOST28147-89 encryption with reverse gamma, 256-bit key (3DES level).
Any of our radio devices operates in the notification (notification) mode, not polling, that is, as soon as an event occurs, it is immediately transmitted to U-PROX. In turn, the security center confirms the reception of the data packet by sending a response. The communication is two-way, imitation-resistant: the packet contains the detector serial number and the packet sequence number, which makes it impossible to replace the detector or send the same data packet by an intruder.
The detector periodically sends data about its status to U-PROX, notifying that it is “alive”. We call this a “heartbeat”. In response, it receives confirmation and additional commands.
If the detector is installed in a place with poor conditions, it is used:
In turn, the basic U-PROX device has 2 transceivers that work simultaneously to receive signals on different channels and speeds. And of course, there is a definition of radio jamming.
Your device communicates with the security company via two GPRS/LTE channels and the Internet – Wi-Fi or Ethernet.
If you try to “jam” or somehow block the communication channel, U-PROX will send a signal informing you.
Yes, if the security system uses the U-PROX PIR Cam detector with photo fixation.
Thanks to it, users of the U-PROX Home mobile application can receive a photo from the detector at any time by pressing one button.
Also, when a photo is received on request, it is possible to save it to the user’s smartphone photo gallery and enlarge it if necessary.
The owner of the security system can also configure permissions to send photos in case of an alarm to security companies.
Wi-Fi is a wireless technology for connecting devices to the wired Internet.
It is implemented in all security centers (hubs).
The central unit in this case can be placed anywhere.
The use of mobile applications U-PROX Home and U-PROX Installer allowed to separate system settings and management.
The U-PROX Home application is used to control the U-PROX security system. The application implements the required set of functions:
U-PROX Installer is used to configure the security system. Through an application is performed the primary activation of the sensors
The security group is a logically independent unit in the security system.
It combines a group of sensors, which is placed and removed from protection separately and independently of others.
This can be done by a user who is authorized to manage a specific group.
This is a function that can work in any of the security groups.
It is implemented as follows. Consider the example of the house. When people put guards in this mode, the sensors that protect the perimeter: doors, windows, or even the entire first floor – become active. Other sensors – indoors – inactive. So, you can move freely inside the room, and intrusion from the outside will be detected.
The sensors are powered by their own batteries.
And the U-PROX security center is equipped with a lithium-ion battery, which will provide autonomous power for 24 hours.
And if this is not enough, then you can use the design feature of U-PROX devices – an input power supply of 12V DC, which means that an external uninterruptible power supply can be used, or a car battery, then the autonomous life can be increased, even up to several weeks.
It is very easy to install the U-PROX security system. Everything you need for installation: screws, fasteners, come complete with each sensor. The devices have simple mounts. Installation of the sensors to the required space can be done using screws or using two-way tape.
The overall security system installation will take about 10-15 minutes.It is very easy to install the U-PROX security system.
Everything you need for installation: screws, fasteners, come complete with each sensor. The devices have simple mounts.
Installation of the sensors to the required space can be done using screws or using two-way tape.
The overall security system installation will take about 10-15 minutes.
This is implemented using cloud technology.
With the security panel, the system works directly, “without intermediaries”.
With the user’s smartphone, the mediator is the cell of the device in the cloud, through which events are displayed on the smartphone and control commands from the user are passed.
Modern systems work via an Internet connection, this is mobile Internet in LTE networks or fixed cable.
U-PROX uses both connections, thus providing data transmission redundancy to the monitoring station in case of blocking or jamming of GSM-communication or cable breakage.
Control of communication with the device is provided by the monitoring panel.
You can prevent water leaks in your apartment or house thanks to automation devices from U-PROX. The flood prevention system warns you of an unwanted water leak in the U-PROX Home app and automatically shuts off the water supply in case of a pipe burst or a malfunction of the washing machine.
The smart valve control and power supply device allows you to automatically shut off/open the water supply when arming/disarming the room.
You can also create personalized schedules for arming/disarming/operating the relay/water valve.
We use a proprietary technology called “U-PROX BAND”, it operates in the 868.0-868.6 MHz frequency range allocated for such systems and transmitter powers allowed without licensing up to 25 MW in the basic device, up to 20 mW in detectors, 10 mW in key fobs, with dynamic adjustment (the first exchange attempt is always at minimum power).
U-PROX BAND has significant advantages over its competitors: the length of the packets transmitted over the air is almost two times less, the optimized retry algorithm (energy consumption-wise), the sensitivity of the detector receivers is higher (this is the range both in line of sight and in building conditions). The U-PROX security center has two transceivers operating at different frequencies in the permitted range, providing redundant data transmission from sensors.
One of the “tricks” of U-PROX BAND is the function of updating the software of all elements over the air. If any shortcomings are corrected or the functionality of the device is added, then the owner and the security company do not need to worry about dismantling, sending for an update. The update will occur automatically after the automatic update of the basic device.
The U-PROX security system has a refined design.
As standard, the cases of devices are executed either white or black.
For WDC sensors, the white starter kit includes replaceable dark brown housings.
If the animal is no more than 25 kg, then we will install special sensors that do not react to such animals, it is not required to restrict pets in movement.
If the animal is large, then we recommend allocating a space for it in the room, where sensors that react to movement will not be installed. There, you can install a sensor that responds to glass breakage, or sensors for opening doors and windows.
You can install the U-PROX Security System even if you have no wired internet.
Since the backup communication source is the LTE/GSM network (the mobile operator card is installed).
But in this case, you lose one of the communication channels.
If the phone is out of network, the security system remote control and watch events will not work.
But you can get an alarm notification if you set up a call from the device to the user’s phone. This mode is indispensable if the system operates autonomously, without remote monitoring.
We advise you to entrust security only to specialized companies, which will monitor your facility 24/7 and respond in case of alarm notification.
U-PROX is the best wireless device for remote protection.